Cyera blog
Thank you! Your submission has been received!
Oops! Something went wrong while submitting the form.
May 21, 2026
What Really Defines a Top AI Security Vendor Today
Thought Leadership
May 21, 2026
Cyera and Anthropic integrate to bring real-time AI security to Claude Enterprise
Product
May 15, 2026
The Future of AI Data Security: Trends, Tools, and Technologies to Watch
Thought Leadership
May 15, 2026
Claw Chain: Cyera Research Unveil Four Chainable Vulnerabilities in OpenClaw
Cyera Research
May 12, 2026
The AI Worked Perfectly. That Was the Problem.
Product
Thought Leadership
.png)
May 5, 2026
Bleeding Llama: A Critical Memory Leak in the World's Most Popular Local AI Platform
Cyera Research

Apr 30, 2026
The Era of Manual Data Classification is Officially Over
Thought Leadership

Apr 8, 2026
What Keeps CDOs Up at Night: The Visibility Gap
Thought Leadership

Apr 7, 2026
Cyera Research Discovers Docker Authorization Bypass That Silently Disables Security Policies, Enabling Full Host Takeover
No items found.

Apr 6, 2026
Prepare for Mission Drift
Thought Leadership
.png)
Apr 2, 2026
FedRAMP High In Process: Securing Mission-Critical Data with Cyera for Government
Thought Leadership

Mar 31, 2026
RSAC Reflections: Data Is the Foundation for Successful AI
Thought Leadership

Mar 31, 2026
Introducing Data Security Topics: A Smarter Way to Understand Sensitive Data at Risk
Product
Mar 23, 2026
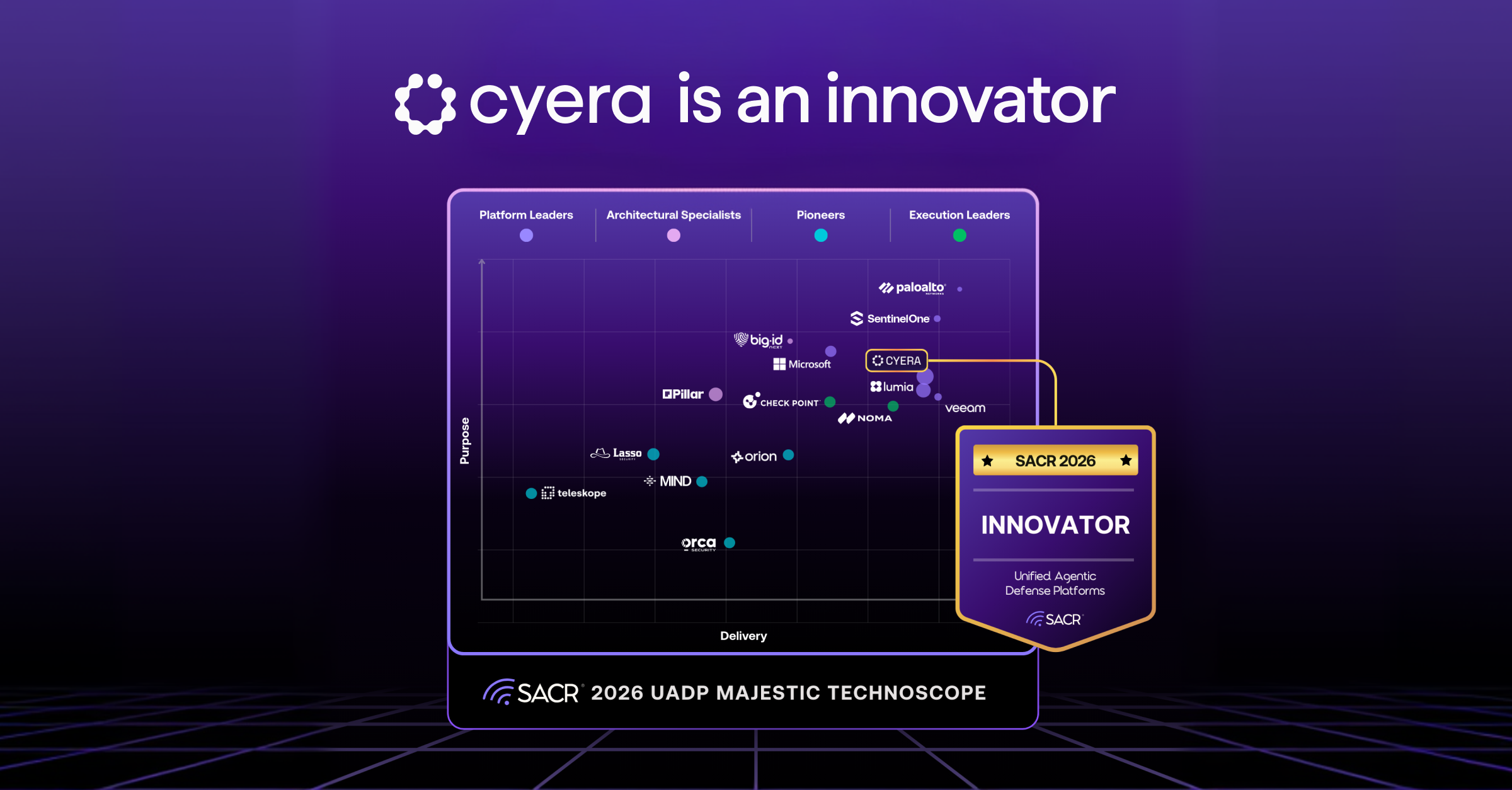
SACR Names Cyera an Innovator in 2026 UADP Technoscope
Thought Leadership
Mar 16, 2026
When AI Security Risks Become Reality
Cyera Research

Mar 16, 2026
From Discovery to Action: Strengthening AI Data Security Without Slowing Innovation
Thought Leadership

Mar 16, 2026
The CDO Advantage: Architecting Value in the Age of AI
Thought Leadership
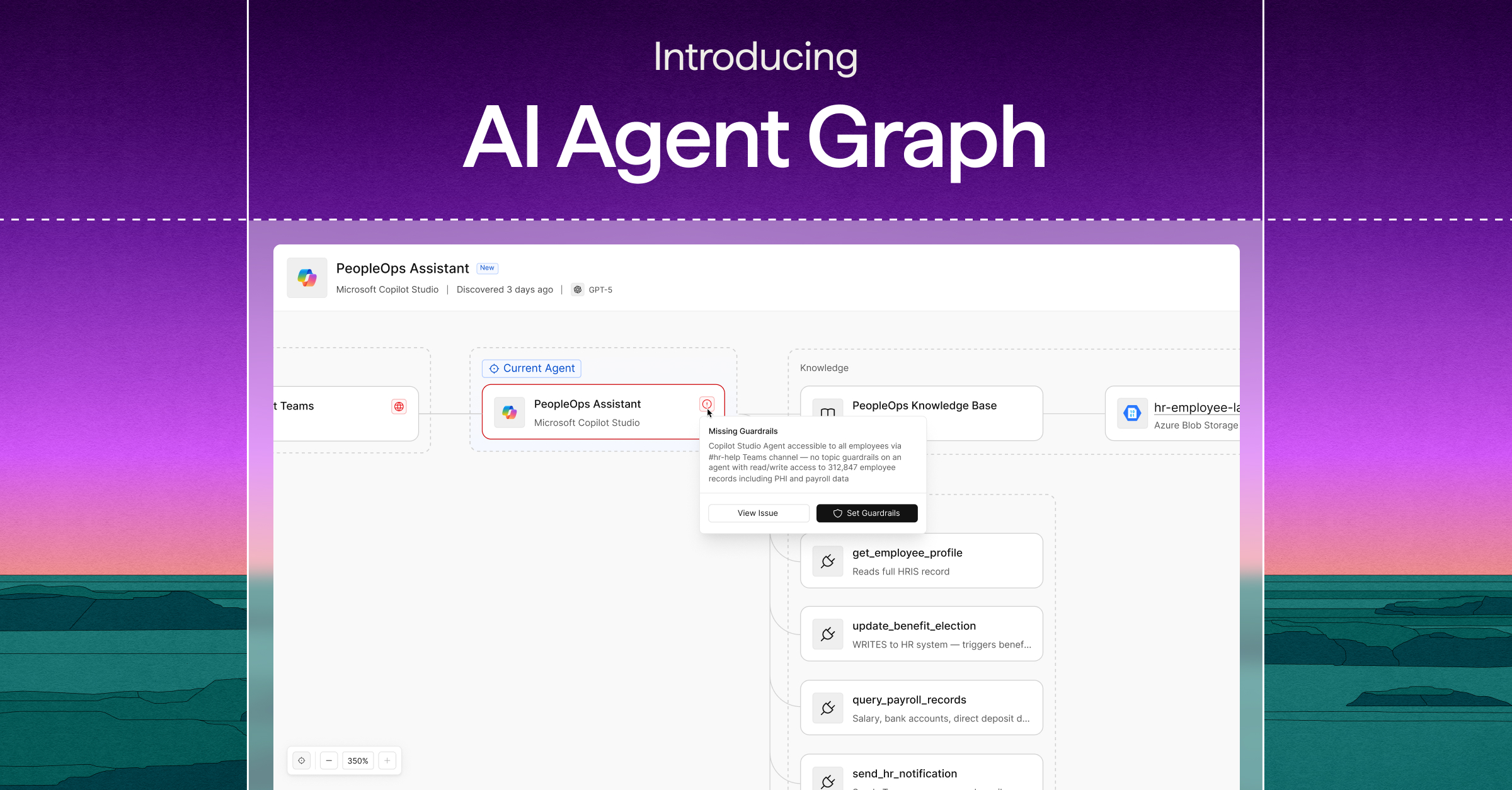
Mar 12, 2026
You Can't Protect What You Can't See: Why AI Visibility Is the New Security Imperative
Product

Mar 2, 2026
The Toxic Combinations of Agentic AI Risk
Thought Leadership
Feb 24, 2026
AI Governance vs. AI Compliance: Why Governance is the Key to AI Security Readiness
Thought Leadership
Cyera Research

May 28, 2026
Agent-Inflicted Damage: Inside the Real-World Failures of Enterprise AI Systems
Cyera Research
.png)
May 15, 2026
Four New OpenClaw Vulnerabilities: When AI Agents Become the Attacker's Execution Layer
Cyera Research
.png)
Apr 29, 2026
SplitSSHell - When a Comma Becomes Root How a Single Character Broke OpenSSH Certificate Authentication
Cyera Research
.png)
Apr 22, 2026
The Data Taxonomy Illusion: Why Security Teams Are Solving the Wrong Problem
Cyera Research
.png)
Mar 26, 2026
LangDrained: 3 Paths to Your Data Through LangChain, the World’s Most Popular AI Framework
Cyera Research

Mar 19, 2026
96% of Enterprise Permissions Go Unused. AI Agents Won't Leave Them That Way.
Cyera Research

Feb 23, 2026
The Long-Lived Risk of Malicious OAuth Applications: A Practical Threat Hunting Guide for M365
Cyera Research

Jan 26, 2026
Cellbreak: Grist’s Pyodide Sandbox Escape and the Data-at-Risk Blast Radius
Cyera Research
Jan 13, 2026
N8Scape (Pyodide sandbox escape): 9.9 Critical Post-Auth RCE in n8n (CVE-2025-68668)
Cyera Research
Dec 23, 2025
Escaping the Guest: How Custom LLM Workflows Uncovered Critical VMSVGA Vulnerabilities
Cyera Research

Dec 22, 2025
Why DSPM Has Moved From Buzzword to Board‑Level Mandate - and How Our New Guide Can Help
Cyera Research

Dec 5, 2025
The One Account That Breaks Everything: How Identity Outliers Create Explosive Risk
Cyera Research

Dec 2, 2025
Access Is the New Exposure: Why Knowing Who Can Reach Your Data Matters More Than Where It Lives
Cyera Research
Nov 25, 2025
Seeing the Forest: Why File-Level Classification Is the Missing Layer in Data Security
Cyera Research
.jpeg)
Nov 17, 2025
From Prompt to Exploit: Cyera Research Discloses Command & Prompt Injection Vulnerabilities in Gemini CLI
Cyera Research
Sep 29, 2025
Smarter at Scale: Why AI-Native Classification Techniques Outperform Exhaustive Scanning

No Results
We couldn't find what you were looking for, try changing the filters








.png)

.png)




.png)










.avif)

.avif)

.svg)