The New Data Breach Playbook: How ShinyHunters Exploit Access
Key takeaways:
- Access is the new exploit. ShinyHunters rarely break systems - they abuse legitimate identity, OAuth tokens, and SaaS integrations to extract data at scale, often without tripping a single traditional defense.
- One compromised identity or vendor can cascade across the entire SaaS stack. Recent incidents (Snowflake, Vercel/Context.ai, Salesloft, the Vimeo leak) show how a single foothold can expose identity, business, product, and analytics data simultaneously - turning a breach into a full blueprint of the organization.
- Defense has to move to the data layer. Endpoint and vulnerability controls are necessary but no longer sufficient. The effective control plane is a unified view of identity, environment, sensitivity, and reachability - knowing where sensitive data lives and who (or what) can actually reach it.
In today’s threat landscape, groups like ShinyHunters are redefining breaches. Their main weapon is abusing legitimate access, trust, and SaaS ecosystems to extract data at scale.
Recent high-profile incidents tied to their name have repeatedly made headlines, from large-scale SaaS data exposures to supply-chain-style compromises. These events highlight not only the impact of their methods,
but also how their brand is now leveraged within the underground to increase credibility and pressure victims.
More importantly, these cases are not isolated - they are blueprints. It is imperative for organizations to study them closely, as they expose systemic weaknesses in identity management,
SaaS integrations, and data visibility. The blog explores what this shift means for defenders, emphasizing why the real battle has moved from endpoints to identity, integrations, and data exposure - where access is the new exploit and data is the ultimate target.
This blog covers who they are, how they operate, and their consistent attack pattern: gaining access via credentials, tokens, or social engineering, then using native platform capabilities to exfiltrate data, often without triggering traditional defenses.
Who Are ShinyHunters?
Below is a brief history, what’s known, and their most notable operations.
Origins and Evolution
ShinyHunters is a well-known cybercriminal collective that emerged around 2019 on underground forums. From the beginning, their activity centered on data theft and monetization rather than destructive attacks.
Unlike ransomware groups that encrypt systems, ShinyHunters built their reputation by stealing large datasets and selling or leaking them on underground marketplaces.
They quickly gained visibility due to the volume and scale of their leaks. Early activity suggests a mix of opportunistic breaches and access acquired through underground trading. Over time, however, their operations matured into a more structured model focused on:
- High-value SaaS and enterprise targets
- Large-scale customer databases
- Extortion campaigns ("pay or we leak/sell your data")
The group is often loosely connected to broader cybercrime ecosystems, including actors involved in credential theft, access brokerage, and identity-based attacks. In more recent investigations, activity attributed to ShinyHunters has been linked to campaigns resembling those of LAPSUS$-style operations, emphasizing social engineering and identity compromise over technical exploitation. This group called SLSH (a.k.a Scattered Spider, LAPSUS$, and ShinyHunters).
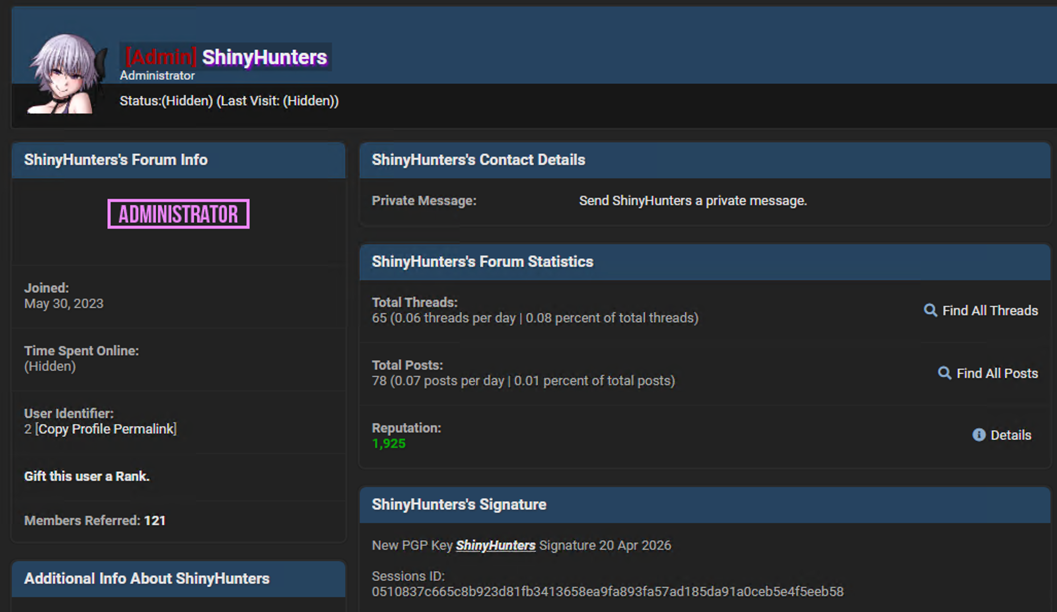
ShinyHunters is particularly interesting right now because, as of March–April 2026, the name is at the center of an open conflict. On one side are the BreachForums operators using the ShinyHunters identity; on the other, a “leak-or-pay” extortion site operating under the same name. Both claim to be the legitimate group, both accuse the other of impersonation, and both have escalated the dispute by leaking data about one another.
BreachForums has been run by many fakes, but not by us anymore, following the FBI seizure on 10 Oct 2025. We (real ShinyHunters group) also do not operate on any Telegram platform or leak forum platforms. People claiming to be us are fake, impersonators, and scammers. Including breachforums.ai being a scam and a fake.
Maintaining such an ecosystem is a waste of our time. There was an unauthorised leak on 9 Jan 2026. Ever since then, false personas going by "N/A" and "Indra" were successfully able to restore a similar-looking "legitimate" forum.
All the current forums are fake [.ai, .sb, .ac, .fi, .bf, .us, etc.]. If they continue to exist, we'll leak all the BF backups, including every private message, emails, IP addresses, posts, etc. We have exploits for all 1.8 versions of MyBB.
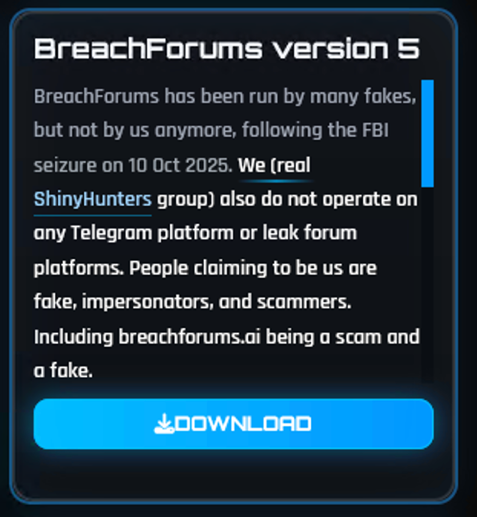
Maintaining such an ecosystem is a waste of our time. There was an unauthorised leak on 9 Jan 2026. Ever since then, false personas going by “N/A“ and “Indra“ were successfully able to restore a similar-looking “legitimate“ forum. All the current forums are fake [ .ai, .sb, .ac, .fi, .bf, .us, ect.]. If they continue to exist, we'll leak all the BF backups, including every private message, emails, IP addresses, posts, ect. We have exploits for all 1.8 versions of MyBB.
Dow
Modus Operandi: What Is Known
ShinyHunters is not defined by a single malware family or exploit. Instead, their strength lies in access and data extraction. Across multiple incident response (IR) investigations, several consistent patterns emerge:
- Identity-first intrusion: Compromised credentials, session tokens, or OAuth access are frequently the entry point.
- SaaS and cloud abuse: Rather than breaching infrastructure, attackers leverage legitimate APIs and export features in platforms like CRMs, databases, and analytics systems.
- Mass data exfiltration: Once inside, the focus is rapid and large-scale extraction of structured datasets (users, emails, phone numbers, financial or behavioral data).
- Monetization through leaks and extortion: Data is either sold on forums or used to pressure victims into paying to prevent public release.
This model reflects a broader industry shift: attacking the data layer through identity and access rather than exploiting software vulnerabilities directly.
How Do ShinyHunters Get In?
ShinyHunters’ initial access is usually not “exploit a database server”. It is more often identity/access abuse that leads to database or SaaS data theft.
General initial access pattern
The best public IR-backed picture is:
- Stolen credentials: Often from infostealer logs, reused passwords, contractor machines, or previously compromised accounts. In Snowflake-related intrusions, Mandiant reported access through stolen customer credentials, often without MFA, not a Snowflake platform vulnerability. In April 2026, Vercel disclosed a breach where attackers gained access to internal systems after first compromising a third-party AI service (Context.ai) and abusing overly permissive OAuth integration to take over a Vercel employee’s account. Context.ai was breached thru a developer who downloaded an infostealer infected tool (disguised as Roblox cheats), allowing attackers to steal session data, including OAuth tokens. The threat actor (ShinyHunters) attempted to monetize the incident by advertising the allegedly stolen data for around $2 million on underground forums, although the real group denied involvement, suggesting the name was used to boost credibility rather than reflect the true operator behind the intrusion.
- Vishing / social engineering: In the Salesforce campaigns, Google/Mandiant tied ShinyHunters-branded activity to phone-based social engineering where attackers impersonated IT support and tricked employees into authorizing malicious connected apps or giving SSO/MFA access.
- Misconfiguration exposure: In campaigns linked to ShinyHunters, attackers exploited misconfigured Salesforce Experience Cloud/Aura setups where guest users and public APIs were overly permissive. Without credentials or malware, they queried these exposed endpoints to extract large volumes of data, demonstrating how simple misconfigurations can enable full-scale data theft without a traditional breach.
- Victim-branded phishing infrastructure: ShinyHunters deploy company-specific SSO phishing pages (e.g., companyname-sso.com) combined with phone-based social engineering to trick employees into providing credentials and MFA codes. Rather than relying on generic phishing, this tailored approach increases trust and success rates, allowing attackers to gain legitimate access and often register their own MFA device immediately, establishing persistence from the outset.
- Third-party / integration compromise (token theft): ShinyHunters compromise SaaS integration providers (e.g., Salesloft, Gainsight, analytics platforms) to steal OAuth or refresh tokens, which are then reused to access hundreds of downstream customer environments. Incidents involving integrations like Drift (via Salesloft) and Gainsight demonstrated how a single vendor compromise can cascade into large-scale access across multiple organizations, making this one of the most scalable and impactful initial access vectors observed.
Databases in particular
For databases, ShinyHunters-style access usually falls into four buckets:
- Cloud database credentials from stealer logs: For instance for the snowflake compromise, ShinyHunters utilised valid usernames/passwords, sometimes old credentials, no MFA, weak IP restrictions, and highly privileged accounts. Once inside, the actor queries/export tables at scale.
- SaaS “database” theft rather than DBMS compromise: Salesforce, CRM, analytics, ticketing, marketing, or customer-support platforms are treated like databases. Initial access is identity-based, then data is pulled through legitimate APIs/export features.
- Public or misconfigured database/API exposure: ShinyHunters has been associated with large exposed-data theft where the root cause often appears to be exposed databases, unsecured cloud storage, or overly permissive APIs. The public record is often weak on exact root cause, but the pattern is “find exposed data plane, exfiltrate, sell/extort.”
- Third-party/vendor access path: ShinyHunters frequently benefit from compromise of SaaS providers, integrations, contractors, or data processors. The victim may see “our database leaked,” but initial access may have occurred through a vendor token, integration, CRM tenant, analytics provider, or employee identity.
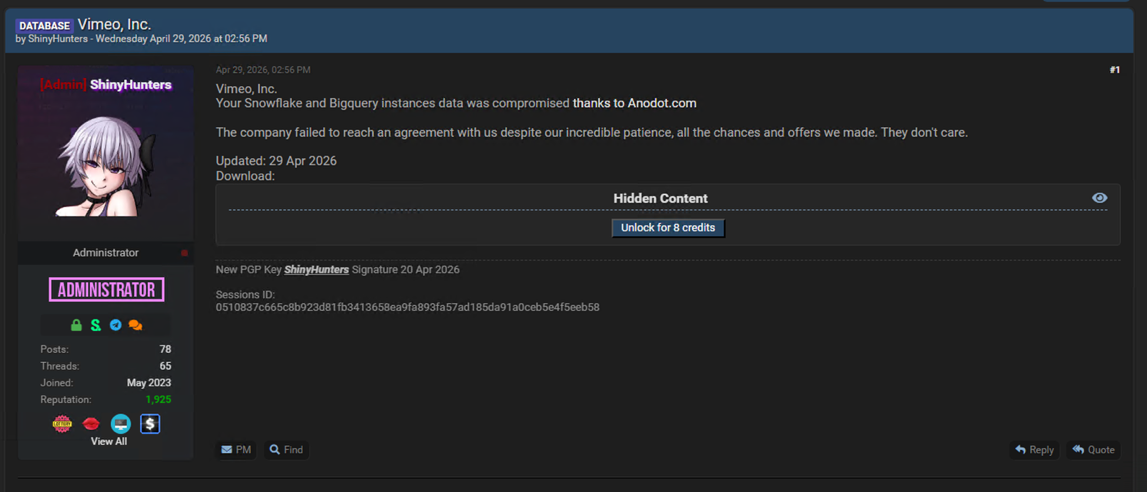
A case study - Vimeo Snowflake and BigQuery Breach (April 2026)
The Vimeo dataset publicly leaked on April 29, 2026. It is a multi-layered exposure across the entire SaaS stack, including user identity, business operations, product analytics, and content metadata.
At the identity layer, large datasets such as active users and registration logs contain user identifiers and behavioral signals, enabling attackers to build detailed user profiles.
At the business layer, datasets from Salesforce core and sales and conversion tables expose revenue pipelines, customer relationships, and deal intelligence. Combined, this creates a powerful foundation for targeted phishing, account takeover, and business email compromise (BEC),
where attackers can operate with high precision and credibility. Fallen into competitors' hands, this data can drastically cripple the organization by providing invaluable competitive business intelligence to rivals.
From a defender's perspective, the most concerning aspect is how these datasets interconnect. Product analytics and telemetry data (funnels, cohorts, feature usage) reveal exactly how users interact with the platform,
while content and streaming datasets (clips, playback history, lifecycle data) expose what users create and consume. In addition, a table called API data also poses a significant threat to the organization.
This allows adversaries to craft highly contextual and believable attack scenarios, mimicking real workflows and user behavior.
In parallel, marketing and attribution data provide insight into campaigns and acquisition channels, enabling attackers to align phishing or fraud campaigns with legitimate business activity and dramatically increasing success rates.
Ultimately, this breach illustrates how a compromised data ecosystem can pose a significant threat to the organization and its customers. The attackers gained access, exfiltrated the data, set an ultimatum, and leaked the data once the ultimatum passed -
publishing to the wild a complete blueprint of the organization, including its users, revenue engine, and operational logic.
ShinyHunters Position in the Modern Threat Landscape
ShinyHunters represents a shift in cybercrime from “breaking systems” to “abusing access.”
Their operations highlight three important trends:
- Data is the primary objective: ShinyHunters campaigns revolve around data. Their utmost desired impact is getting paid for exfiltrated data or leak it.
- Identity is the weakest link: Credentials, tokens, and SaaS permissions are often easier to exploit than software vulnerabilities.
- Scale through ecosystems: By targeting SaaS platforms, integrations, and cloud environments, attackers can access massive datasets from a single-entry point.
Why They Matter
ShinyHunters is not just a single group. It’s a “business” model of modern data-centric cybercrime. Threat actors like TeamPCP, Lupsus and many others. Successfully demonstrate how attackers can:
- Operate without deploying malware
- They only relay on compromised or misplaced keys and social engineering
- Blend into legitimate user activity
- Exploiting overly permitting access
- Extract enterprise-scale datasets in hours
- Monetize breaches rapidly through underground markets
Implications for Defenders: Securing Identity, SaaS, and Data
The attack surface has fundamentally changed. The campaigns associated with ShinyHunters clearly demonstrate that. Their “known associate” and copycats strengthen that claim even further.
Cybercriminals neglect exploits and malware. They are leveraging legitimate access, abusing integrations, and extracting data through normal platform functionality. The underground market support that with dozens of sources that trade infostealer logs, phishing logs, and others.
Traditional defenses centered on endpoints and vulnerabilities are necessary, but no longer sufficient. The real control point has moved to identity, SaaS ecosystems, and most critically - the data itself!
Identity Is the Entry Point-but Not the End of the Story
Strong identity controls are only the first layer. Even when attackers gain valid access (through stolen credentials, OAuth abuse, or social engineering) the real question becomes:
What can they reach from there?
This is where many organizations lack visibility. It is not enough to secure authentication. Defenders must understand how identity maps to data access across cloud and SaaS environments.
SaaS and Data Sprawl Create Invisible Risk
Modern environments are highly fragmented:
- Cloud data stores,
- SaaS platforms,
- Analytics tools,
- and third-party integrations all interconnected.
All of these are interconnected. Sometimes these are just the basics, and each connection expands the potential blast radius. Attackers exploit this complexity by moving through trusted relationships. They access sensitive data not by escalation, but by following the same paths legitimate users and applications already use.
Without a unified view, organizations cannot answer a basic question: where is my sensitive data, and who can access it - directly or indirectly?
Data Is the Real Control Plane
These attacks primarily target data. And yet, most defenses are still not built around it. A data-centric approach shifts focus to:
- Discovering and classifying sensitive data across environments
- Understanding exposure based on access, not just location
- Continuously mapping who (and what) can reach that data
This includes identities, roles, applications, and integrations. Forming a complete picture of effective access, not just configured permissions.
Detecting Risk Before It Becomes a Breach
Before you deploy anomalous behavior, sensors and identify large-scale exfiltration, you need to identify risk conditions early:
- Overexposed sensitive datasets
- Excessive or unnecessary access permissions
- Third-party integrations with broad data reach
- Dormant or forgotten access paths
By continuously analyzing these factors, monitoring them, and addressing these issues, organizations can reduce the attack surface before an attacker ever logs in.
The New Defensive Model
Security moves from protecting systems to understanding and controlling data exposure in context. This means correlating:
- Identity (who has access)
- Environment (where the data lives)
- Sensitivity (what the data actually is)
- Reachability (how it can be accessed)
When these dimensions are unified, defenders gain something they previously lacked: a real-time understanding of data risk across the entire organization.
In a world where attackers use valid access and legitimate tools, the only effective defense is to know your data deeply, continuously, and in context, and to control access accordingly.
How Cyera Can Help
The campaigns described above share a common thread: organizations rarely have a continuous, contextual view of where their sensitive data lives, who and what can reach it, and how that exposure shifts over time. Closing that gap requires moving beyond perimeter and endpoint controls toward a data-centric model - one that unifies identity, access, sensitivity, and reachability into a single picture of real risk.
This is the problem Cyera is built around. By continuously discovering, classifying, and contextualizing data across cloud, SaaS, and on-prem environments - and correlating it with identity and access - the goal is to give defenders visibility into exposure before attackers find it, and clarity on what to remediate first. For more on how a data-centric approach maps to the kinds of identity- and SaaS-driven campaigns described here, see our Data Security Posture Management platform.
.avif)
.png)
.png)
.png)

.svg)