Compromise Once, Breach Everywhere. The Age of Mega-Supply Chain Attacks

The Age of Mega-Supply Chain Attacks
Key Takeaways:
- A breach at AI analytics firm Context.ai cascaded into unauthorized access inside Vercel - exposing employee data and potentially impacting hundreds of organizations through a single compromised OAuth integration.
- Attackers, attributed to ShinyHunters, are no longer breaking into systems one by one. They are exploiting trusted AI and SaaS integrations to inherit access across entire ecosystems simultaneously.
- This is the defining threat pattern of 2026: compromise a single high-trust layer - an AI tool, a security scanner, an identity provider - and scale that breach across every organization it touches.
In April 2026, Vercel disclosed what initially appeared to be a contained security incident involving unauthorized access to internal systems.
But beneath the surface, this was not just another breach.
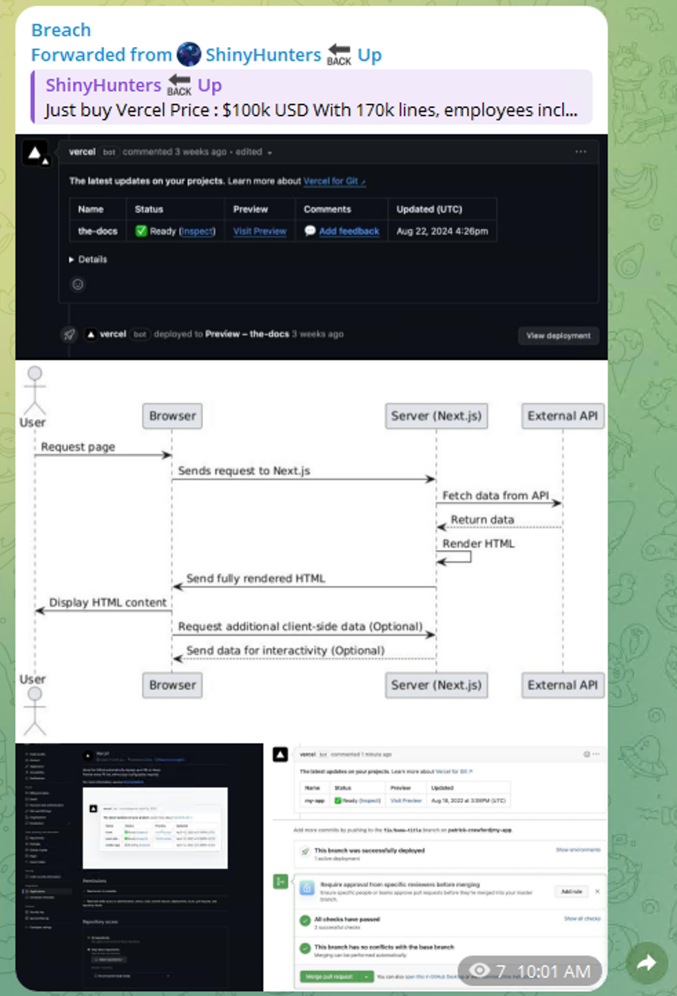
It was a signal of a deeper shift in how modern attacks unfold. The incident was not driven by a traditional vulnerability, but by the compromise of a trusted AI integration, turning a productivity tool into an attack vector.
This event, combined with parallel supply chain compromises seen earlier in the month, highlights the emergence of a new reality: AI and SaaS tools are becoming high-privilege access layers inside organizations. As enterprises increasingly rely on interconnected platforms, attackers are no longer breaking into systems. They are inheriting trust through them. The Vercel case (and Aqua Security’s Trivy) provide a clear lens into this transformation and its implications for security teams.
The Breaches Chain of Events
The company context.ai published a blog saying that they identified and stopped, last month, a security incident involving unauthorized access to their AWS environment. They activated what seems to be the correct incident response protocol by hiring a top-tier security company and contained the event, isolated and restored. Nevertheless, this wasn’t enough something went wrong and one of the OAuth tokens to access that company’s Google Workspace was compromised. That company was Vercel.
Before we continue, a word about Context.ai and Vercel. Both sit at the center of the modern developer ecosystem, where AI and cloud-native workflows are rapidly converging. Context.ai represents a new generation of AI tooling embedded directly into development, data analysis, and operational workflows. It is often with deep integrations into email, code repositories, and internal systems. Vercel, on the other hand, powers a significant portion of the modern web, enabling teams to deploy, manage, and scale applications with minimal friction. Together, they reflect a broader market trend: explosive adoption of SaaS and AI-driven tools that prioritize speed, automation, and seamless integration. This ecosystem is growing fast, driven by developers, startups, and enterprises alike, with adoption often outpacing security maturity.
However, this same convenience introduces a critical risk especially when it comes third-party exposure as an attack surface. Tools like Context.ai are typically granted high levels of access through OAuth and API integrations (exactly as happened in this case), effectively becoming extensions of the organization’s internal environment. When platforms like Vercel rely on or interact with such tools, they inherit not only their capabilities, but also their risks.
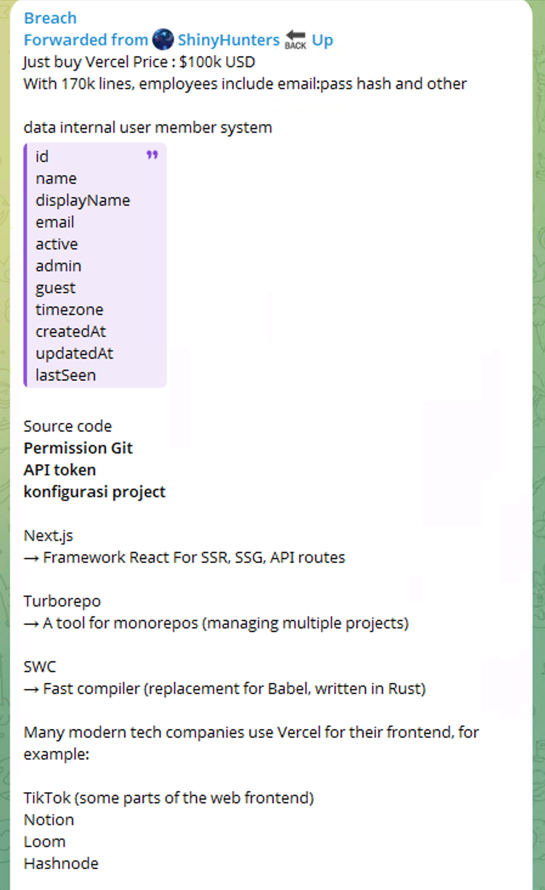
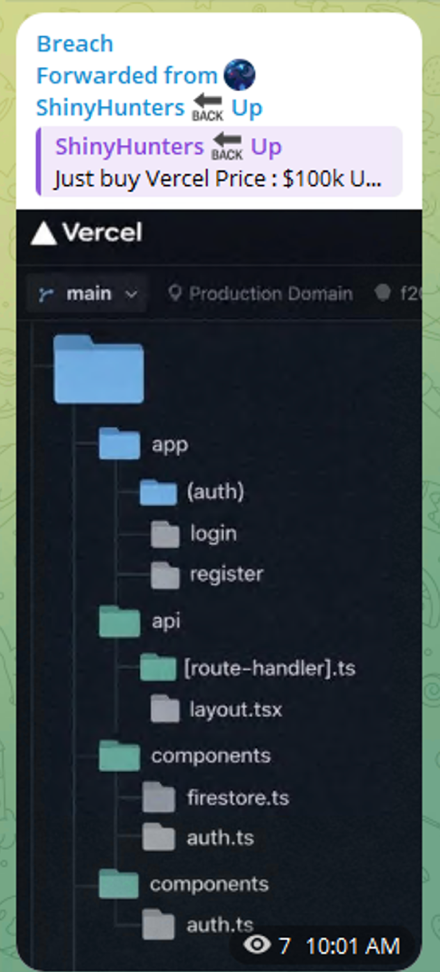
The Vercel incident was published over the weekend ofApril 19th, 2026. The attackers gained trusted access and move laterally into Vercel’s environment, reaching internal data and employee-related information. The impact was twofold. For Vercel, it resulted in unauthorized access to internal systems, exposure of employee-related data (such as names, emails, and activity logs), and a potential leak of non-sensitive environment variables that could still contain operational secrets.
Consequently, a limited subset of customers was affected, and Vercel had to urgently advise users to rotate credentials and audit their environments.
Beyond Vercel itself, the broader impact is more significant. The same compromised AI tool and OAuth app were part of a wider attack that may have affected hundreds of organizations using the same integration. This turns the incident into yet another massive software supply-chain event (along with the Trivy breach mentioned below), where one breach propagates across multiple companies through shared trust relationships.
ShinyHunter, not their First Rodeo
ShinyHunters is one of the most prominent actors in today’s cybercrime ecosystem, operating at the intersection of identity abuse, large-scale data theft, and monetization. Active since around 2019, the group is known for breaching major SaaS platforms and enterprises, extracting massive datasets, and then selling or extorting that data.
Their operations are tightly linked to the underground economy, where stolen data is traded on forums such as BreachForums, which a major marketplace that replaced earlier forums and became a central hub for buying, selling, and leaking breached data.
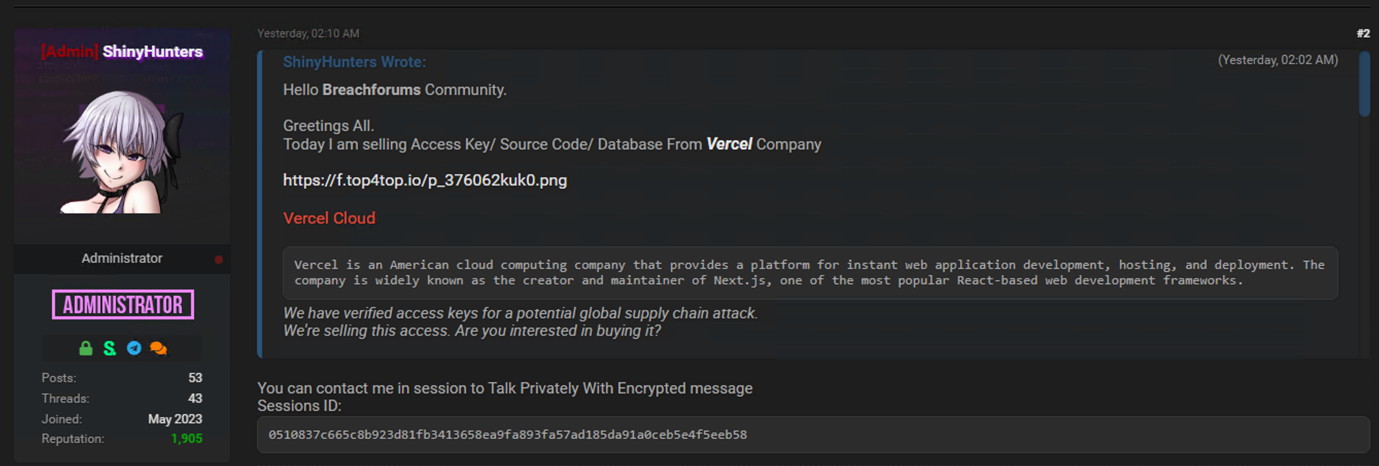
In recent years, ShinyHunters has increasingly shifted toward Telegram-based operations, using multiple channels to announce breaches, share proof samples, and pressure victims publicly. These channels often act as real-time extortion platforms (posting teasers, countdowns, and “pay-or-leak” threats to maximize visibility and impact).
Second Major Supply Chain Attack in April
Earlier this month (April 2026), the industry was already grappling with a major supply chain compromise linked to TeamPCP, where attackers leveraged widely used tooling and shared infrastructure to reach multiple downstream victims. In that case, tools like Aqua Security’s Trivy (commonly embedded into CI/CD pipelines) became part of the broader exposure narrative, illustrating how deeply integrated security and development tools can unintentionally expand the attack surface. Consequently, tools like LiteLLM, Checkmarx and others were also compromised.
A New Attack Pattern: AI-Related Supply Chain Entry Point
The most important takeaway from this incident is not the specific breach, but the attack pattern it represents.
The Vercel incident closely mirrors this pattern, but through trusted tools that enabled a much wider blast radius. Instead of targeting infrastructure directly, attackers compromised high-trust platforms (AI tools like Context.ai and security tools like Trivy) to gain persistent access and pivot into internal systems and customer environments. The Trivy attack was significantly exploded when LiteLLM (3 million daily downloads) was compromised. In both cases, there were indications of earlier exposure, suggesting attackers were able to maintain or re-establish access over time. This highlights a critical shift: attackers are increasingly targeting central, trusted components embedded deep in modern pipelines.
This is where activity attributed to ShinyHunters becomes especially relevant. Their campaigns consistently show how compromising a single trusted layer (whether a SaaS platform, shared tool, or identity provider) can scale across multiple organizations. The connection is clear: modern attacks are no longer about breaching every target individually, but about breaking trust once and reusing it across the ecosystem.
AI tools are increasingly integrated into core enterprise workflows, often with broad access to:
- Source code repositories
- Internal documentation
- Communication platforms
- Cloud environments
These integrations are typically trusted by default and monitored less rigorously than traditional infrastructure.
As a result, compromising a single AI tool can provide attackers with a high-privilege entry point into multiple organizations simultaneously.
This represents a fundamental shift:
From exploiting systems → to exploiting trust relationships.
The Security Gaps This Exposes
The Vercel incident - and the broader pattern it represents - makes several critical gaps impossible to ignore:
Invisible access paths. Organizations frequently do not have a clear picture of what data their AI and SaaS integrations can reach. When a tool is compromised, the blast radius is unknown because the access map was never drawn.
Excessive permissions by default. OAuth integrations are routinely over-permissioned. Convenience-driven onboarding means tools often receive access far beyond what their function requires - and that access is rarely revisited.
Identity sprawl. Each integration creates an implicit trust relationship. Across a modern enterprise, these accumulate into a complex, largely invisible web of third-party access that is nearly impossible to manage manually.
Detection blind spots. Traditional security controls are designed to detect anomalies in systems behavior. They are not designed to detect misuse of legitimate, trusted access - which is precisely what these attacks exploit.
Delayed discovery. In both the Context.ai/Vercel chain and the Trivy campaign, evidence suggests attackers maintained or re-established access over extended periods. The breach had already propagated before it was identified.
What Security Teams Must Do Now
- This threat pattern demands a fundamental shift in security posture - from perimeter-centric and infrastructure-centric thinking to data-centric, access-aware defense.
Concretely, that means:
- Map your AI and SaaS access surface. Every OAuth application and API integration that touches sensitive data is a potential entry point. Security teams need to know what is connected, what it can access, and whether that access is still necessary.
- Enforce least-privilege on third-party integrations. Treat AI tools with the same rigor applied to privileged human identities. Scope access precisely, review it regularly, and revoke it when it is no longer needed.
- Understand your blast radius before an incident. The question after a breach is always "what could they have reached?" That question should be answered in advance, not in the middle of an incident response.
- Monitor for behavioral anomalies in integration activity. Unusual patterns in how a connected tool is accessing data - at odd hours, across unusual resources, in high volumes - should trigger alerts just as a suspicious login would.
- Assume shared tools will be targeted. If a tool is widely adopted and sits at the center of multiple organizations' workflows, it is a high-value target. Design your integration posture accordingly.
How Cyera Addresses This Directly
Cyera is built for exactly this challenge. Where traditional security tools focus on infrastructure and identity, Cyera focuses on data - where it lives, who and what can access it, and what happens when that access is abused.
The core challenge this attack pattern creates is a visibility problem: when a trusted integration is compromised, most organizations can't quickly answer what data was reachable. Incident response stalls. Scope is unclear. Remediation is guesswork.
Cyera addresses this directly by focusing on the data layer - where sensitive data lives across cloud and SaaS environments, how it is classified, and what is actually exposed.
When a third-party integration is compromised, Cyera gives security teams an immediate, accurate picture of what data assets were accessible - not after a forensic investigation, but in real time. That means faster scoping, more precise remediation, and a defensible answer to the question that matters most in the first hours of an incident: what did they have access to?
Beyond incident response, Cyera continuously identifies unnecessary data exposure and misconfigurations - reducing the available attack surface before an integration is ever targeted.
In a threat environment defined by inherited trust, knowing exactly what data is at risk is the foundation everything else depends on.
Comprehensive data visibility. Cyera provides deep, continuous visibility into sensitive data across cloud and SaaS environments. When a third-party integration is compromised, security teams have an immediate, accurate picture of what data was reachable - not a guess.
Access path mapping. Cyera maps how data is accessed, including through AI tools and SaaS integrations. This exposes excessive permissions, hidden exposure points, and trust relationships that would otherwise remain invisible until they are exploited.
Blast radius quantification. In the event of a compromise, Cyera enables teams to rapidly determine which data assets were accessible through the affected identity or integration - dramatically accelerating response and scoping remediation efforts with precision.
Proactive risk reduction. Cyera continuously identifies misconfigurations, over-permissioned identities, and unnecessary data exposure before they become incident triggers. In a threat environment defined by trusted-access abuse, reducing the available attack surface is the most effective form of prevention.
The ability to answer "what could an attacker have accessed through this integration?" - instantly, accurately, and continuously - is no longer a nice-to-have. It is the foundation of defensible security in the era of mega-supply chain attacks.
Conclusion
The Vercel incident is not an isolated case; It is part of a broader evolution in cyber threats. Attackers are shifting away from exploiting code and infrastructure, and instead focusing on trusted integrations, identity layers, and shared tools that sit at the center of modern environments. Whether through AI platforms like Context.ai or widely adopted tools like Trivy, the strategy is the same: compromise once, scale everywhere.
This shift demands a fundamental change in how organizations approach security. Visibility into data, control over access paths, and an understanding of trust relationships are now critical. In a world where AI is deeply embedded into operations, the question is no longer if these tools will be targeted, but how prepared organizations are when they become the next entry point.
.avif)

.png)

.svg)