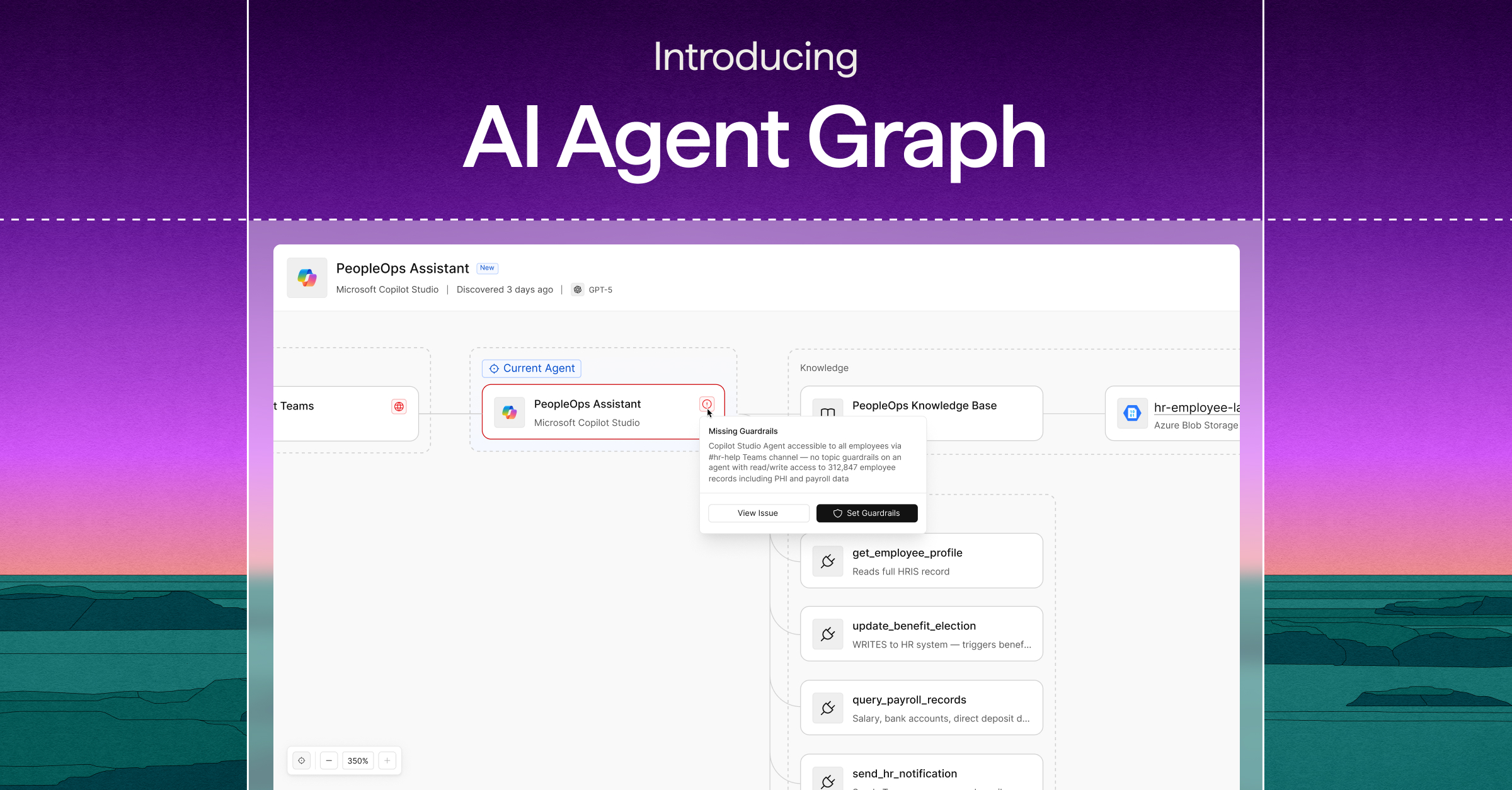
Introducing the Cyera Agent Graph: The surveillance layer for Agentic AI
The Cyera Agent Graph unifies data, identity, and application context into a single, traceable view - giving enterprises the control plane for securing Agentic AI.
It's a Tuesday morning. Your developers shipped three new AI agents. Legal approved one. IT knows about two.
One is pulling customer contracts to draft renewal summaries. One is reading support tickets from your ticketing system and writing responses. One (this is the one nobody's quite sure about) is somewhere in your data environment doing something useful, probably.
2 weeks later, and the initial scope of data and tools these agents were built to use has completely drifted. And your Security team simply has no answer to one question:
Are these agents accessing the data and tools they were designed to?
Today, piecing together this picture means switching between consoles, sifting through alerts, and still missing the insight into:
- who is the agent acting as?
- what tools has it accessed?
- what data has it touched?
By the time you have an answer, the damage is done.
The Cyera Agent Graph is the first unified graph that correlates intelligence from DSPM, DLP, and Identity into how AI agents reach, move, and expose sensitive data. The graph goes beyond the data and brings the agent's identity and tool use to expose risks that security teams would have missed otherwise, enabling them to greenlight more agents across their business, faster.
See the full anatomy of an agent: From intent to behavior
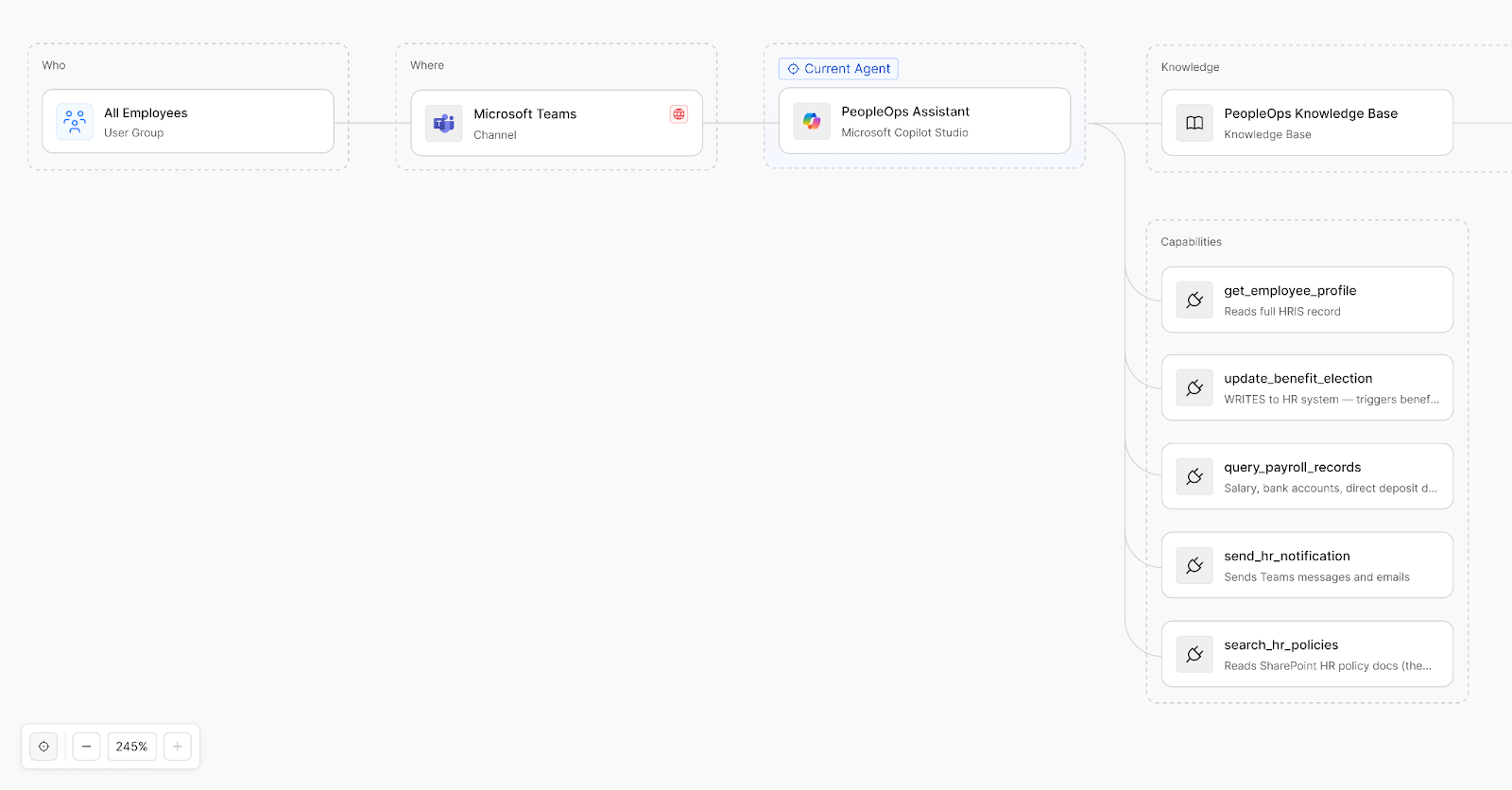
Every agent has an anatomy. A reason for being. A set of parameters about what it knows, what it can do, and how far it's allowed to go.
Until now, security teams had no way of seeing it.
The Agent Graph changes that. It gives you a living picture of every agent in your environment - not a static configuration snapshot or a moment-in-time audit artifact, but a dynamic view that evolves as the agent does. The moment its behavior changes, so does the graph.
What you see goes beyond the technical metadata. It's the full anatomy of an agent:
- Its purpose — what it was built to do and why
- Its composition — which LLMs power it, which knowledge bases it’s connected to
- Its permissions — what actions it's authorized to take, and what it can reach
- Its behavior — what it's actually doing, right now, in the real world
In seconds, you understand the intent behind an agent. And more importantly, you can judge whether its actions match that intent.
This allows you to constantly audit and address the gap between what an agent was designed to do and what it's actually doing.
All agents. One governance model.
Most organizations run agents across Amazon Bedrock, Azure AI Foundry, Salesforce Agentforce, Microsoft Copilot Studio, and more. Every platform uses a different schema, different guardrails, and different logic for how agents access knowledge and execute actions. That forces security teams to learn each platform's nuances before they can even begin a risk assessment.
The Agent Graph removes that burden. It normalizes every agent, regardless of platform, into a single and consistent visual framework. Same security insights. Same investigation workflow. Same governance standards. Whether you're looking at a Bedrock agent or a Copilot Studio agent, the answer to "what is this thing doing?" looks exactly the same.
A single governance model for every agent. No exceptions.
Smarter prioritization of real risks
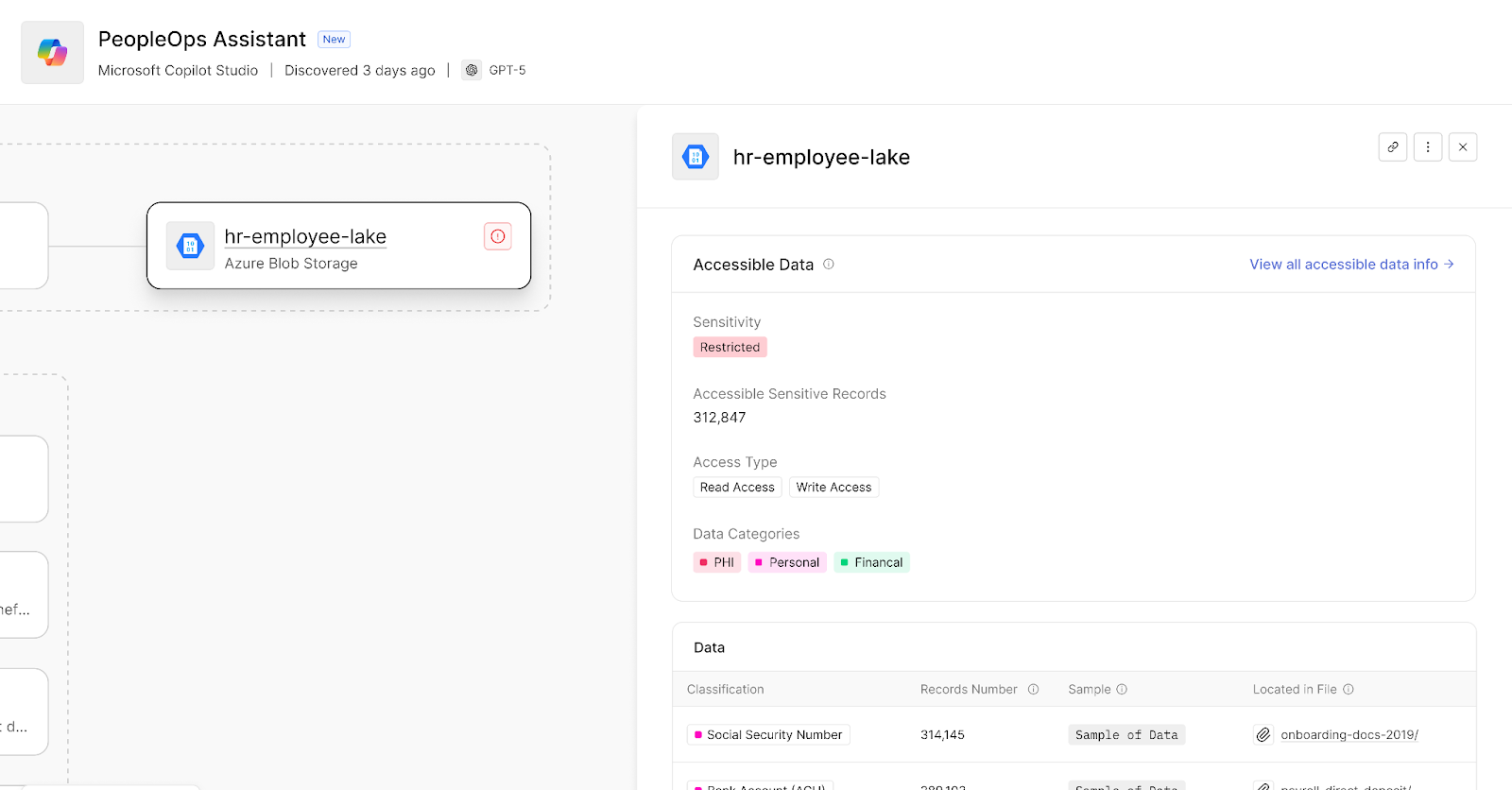
A connection between an agent and data is only a risk if the data itself is sensitive to your organization. Most security tools show that connections exist but cannot tell you what’s on the other end.
Data classification, built into the graph
The Agent Graph integrates directly with Cyera's intelligent DSPM engine. Every connected data store shows its classification: record counts, sensitivity levels, and specific data categories or Topics. If an agent is connected to a bucket containing customer PII or confidential contracts, you see that immediately, not after a separate investigation.
Risk ranked by exposure, not connectivity
This changes how you prioritize. An agent connected to a public knowledge base with no sensitive data is a different conversation than an agent with read access to a database containing 50,000 patient records. The graph makes that distinction obvious so you spend time on what actually matters.
Connect the dots between humans and agents
AI agents frequently use service roles and non-human identities to execute tasks. These identities often carry broader permissions than anyone intended, and they create paths that a compromised agent can follow to access data it was never designed to touch.
Map human users to non-human identities
The Agent Graph traces the relationship between the people who trigger agents and the service identities those agents use to operate. You see which users, Slack channels, or other integrations can invoke a specific agent, and what that agent's service identity can access downstream.
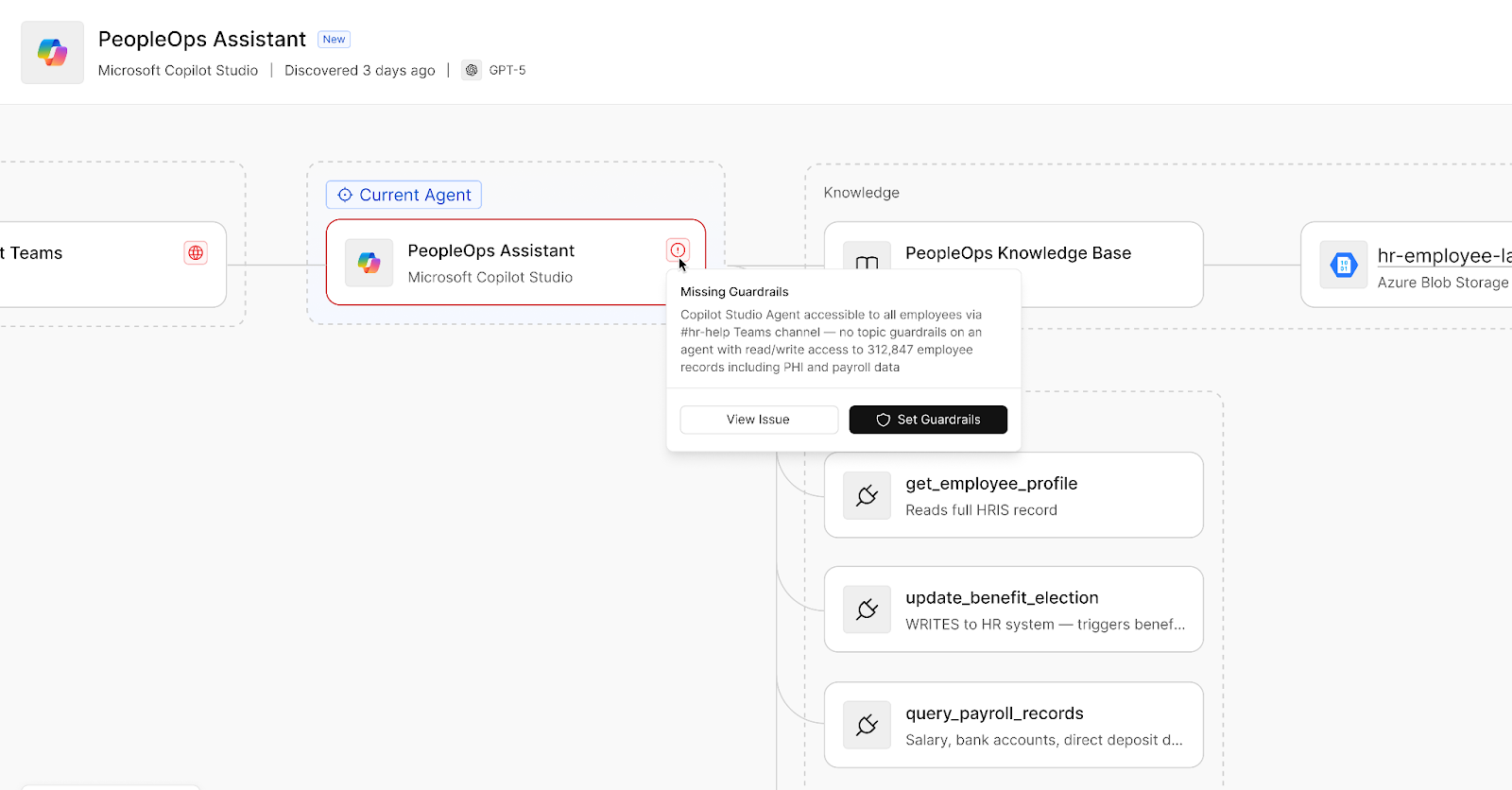
Actionable insights on every policy violation
The Agent Graph surfaces policy violations, such as missing guardrails, overly broad permissions, or soon, leakage and unethical usage alerts, directly on the relevant nodes. When a guardrail is missing or a privilege path looks wrong, the flag appears in context, not in a separate alert queue. That turns a passive inventory into an investigation workspace where you can assess exposure and act immediately.
Getting started
The AI Agent Graph is currently available in beta for existing Cyera customers. To see how it maps your agent anatomy, book a personalized demo and walk through agent governance with the Cyera team.




.svg)