New From Cyera: Smarter Security for AI and the Data it Touches
For a long time, traditional data security played defense. Build walls, write policies, and lock down the places data is “supposed to live”.
Cloud-first work already broke that model and today AI accelerates the gap even further, pushing sensitive information into AI prompts and agent workflows before traditional controls ever see it.
To keep up, security teams must stop chasing data after it moves and start moving with it.
Cyera’s most recent product releases focus on solving five pain points where teams lose time, context, and control:
- Sensitive data entering prompts in web-based AI tools
- Files with sensitive data are multiplying into copies and derivatives by AI
- Security can’t clearly explain risk in business terms, delaying action
- AI systems that are blind to policies before retrieving data
- Privacy operations forced to run on stale inventories
These are connected capabilities designed to give teams continuous visibility and control across the lifecycle of sensitive data.
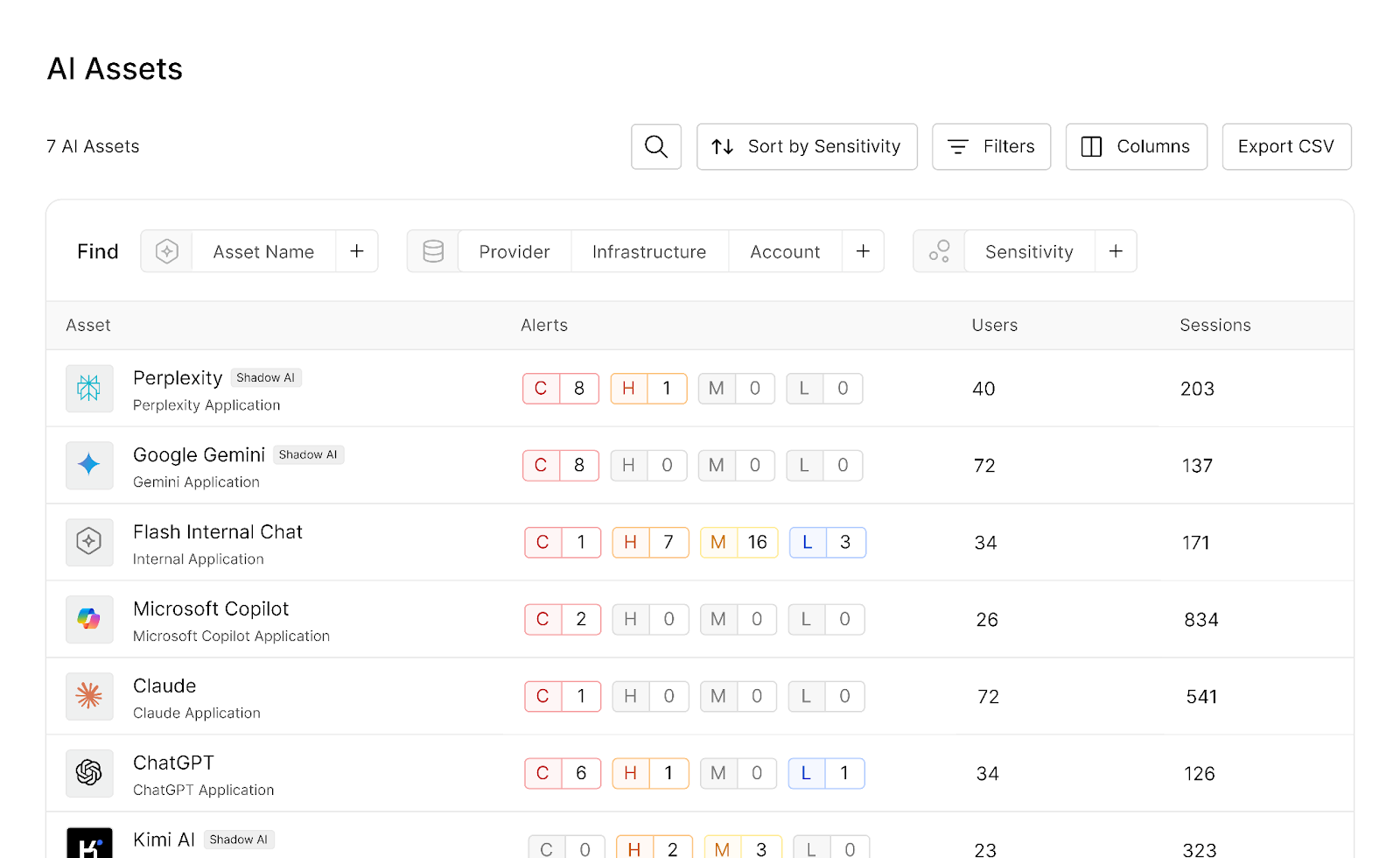
Browser Shield: See and Protect Browser-Based AI Usage in Real Time
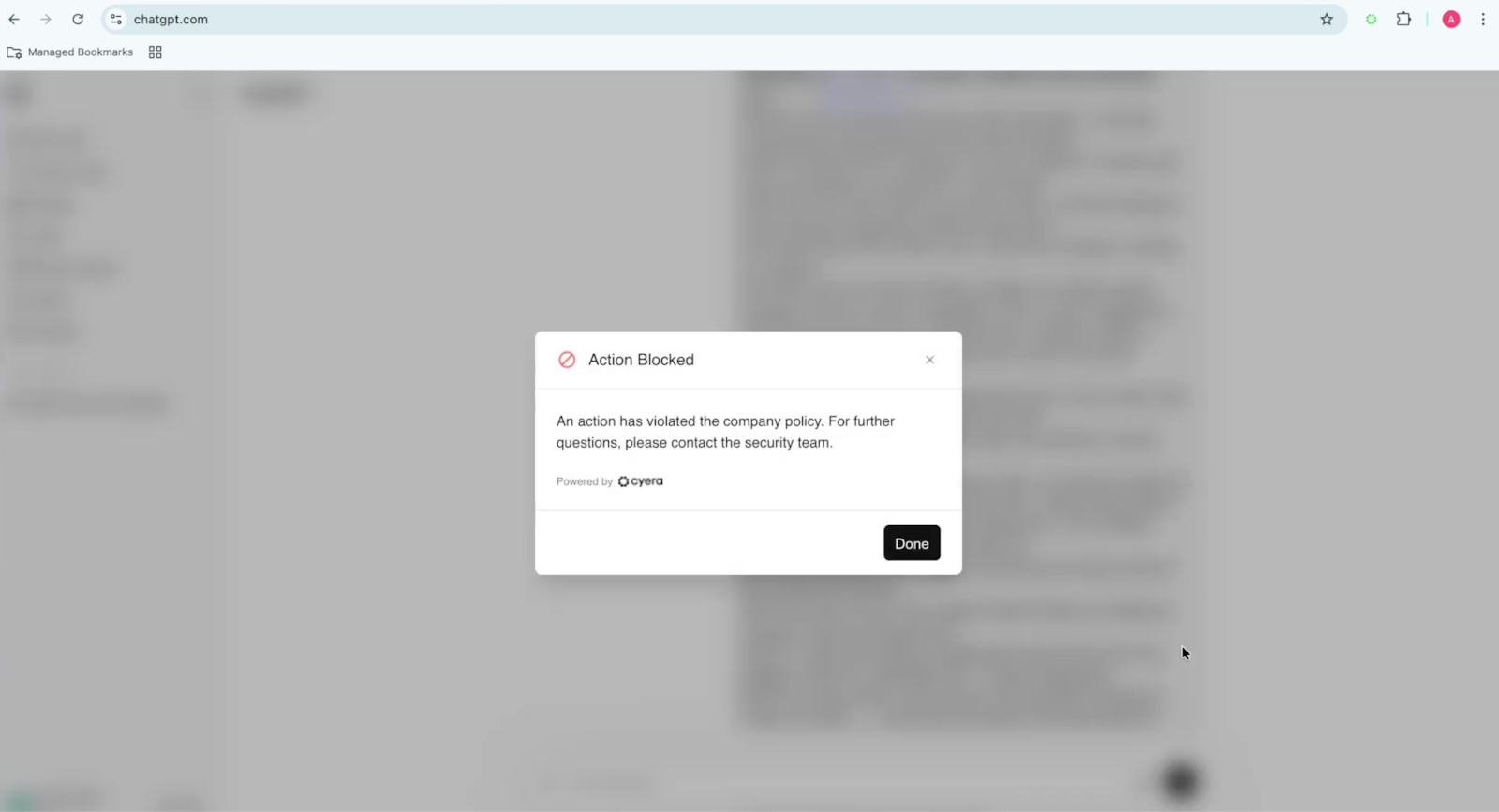
Data exfiltration no longer starts with a misconfigured cloud bucket. It starts with something much simpler: an employee pasting sensitive data into an AI chat window in their browser.
Employees in every department are increasingly adopting AI tools to move faster and become more productive. They paste a paragraph from a contract into an AI chat to “clean up the language.” They drop a customer snippet into an AI tool to “summarize patterns.” They ask an AI companion to “build a full termination plan for a quiet quitter direct report”.
It feels like typing, but AI prompts are data movement.
Most organizations still struggle to answer three basic questions: which AI tools are being used, how, and for what purpose. The controls that worked for email and file shares often fall short in the browser, where traffic is encrypted and context on data, user, and intent matters.
That is exactly where the Cyera Browser Shield operates: it provides an inventory of all browser-based AI tools used in the organization and, when an AI prompt is submitted, real-time visibility and policy enforcement to help teams secure AI usage without slowing work down.
It helps teams:
- Discover which browser-based AI tools employees are using (not just the approved ones)
- Map tools to users and subscription type (anonymous, personal, or corporate)
- Detect sensitive data leakage or unethical use attempts in real time
- Enforce policy with clear actions: block, alert, or allow—before prompt is submitted into public models
This is not about trying to stop AI adoption. Blocking alone rarely works. It is about making AI usage visible, governable, and aligned to real risk by connecting data, identity, intent, and organizational context in real-time, ensuring security and compliance are maintained.
Browser Shield is in early availability. Read the blog to learn more.
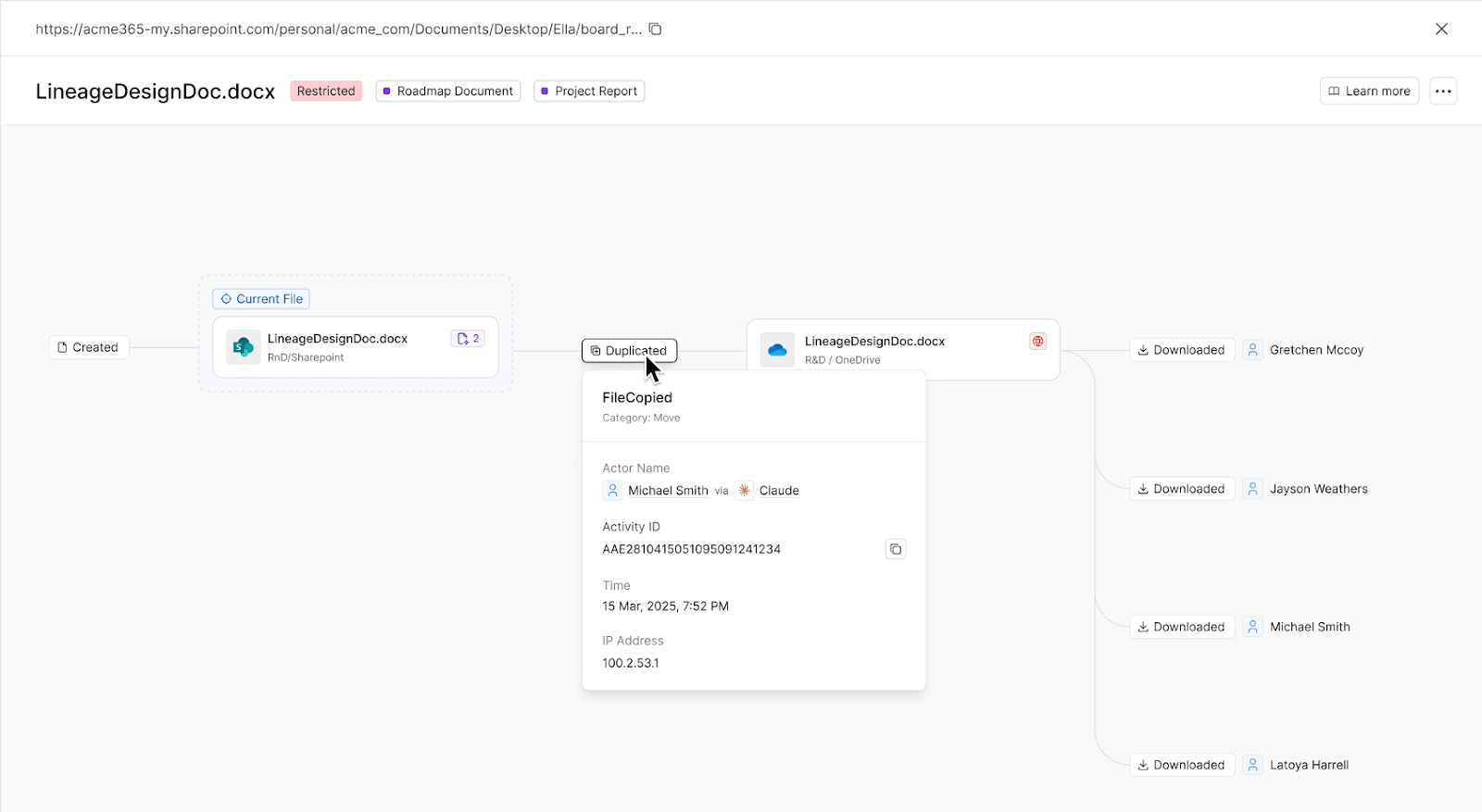
Data Lineage for Files: Track sensitive files across their entire journey, not isolated events
Most security teams are still piecing together individual logs and endpoint activity to understand how incidents transpire.
A financial model is created in SharePoint. Someone downloads it to OneDrive to work faster. A revised version gets uploaded to a different folder. A summary is exported and shared externally. Now there are multiple versions across multiple systems, with no audit trail connecting the events.
Traditional activity monitoring can tell you that things happened. It often cannot tell you whether it was the same file, how it propagated, or what the true blast radius is. And in incident response, the first file is rarely the only one that matters.
Cyera’s Data Lineage for Files connects the dots and shows the story of the file, not just individual events. It maps how sensitive files spread as a living graph: who copied what, where it went, and how it multiplied into variants.
Because sensitive files move quickly, File Lineage can help identify likely related “rogue” copies using content similarity, including versions recreated via copy/paste or modified to bypass typical tracking.
Teams use this context to understand exposure quickly and resolve incidents with confidence.
Data Lineage for Files is in beta. Read the blog to learn more.
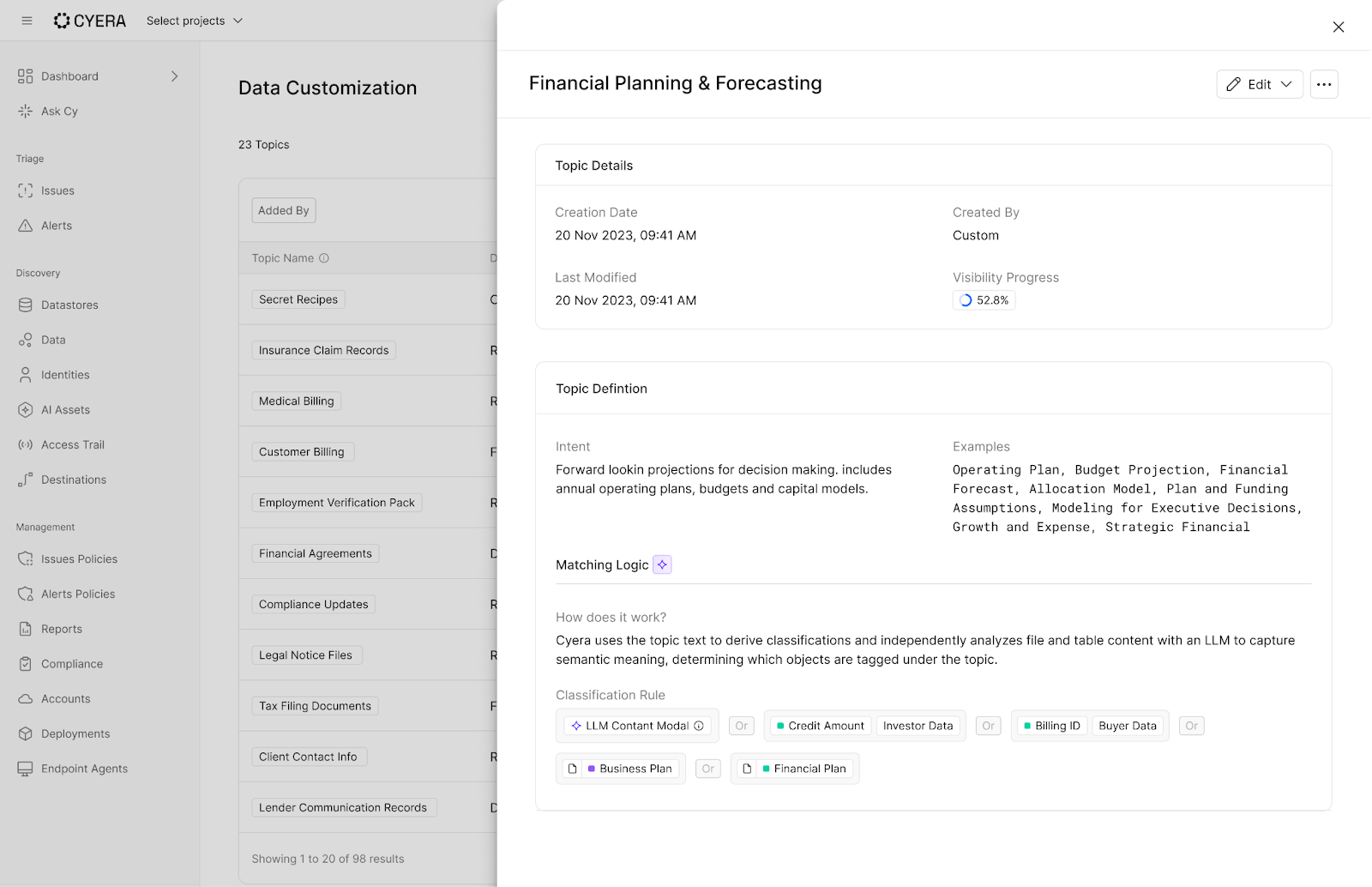
Classification Topics: Prioritize what your business actually cares about
Cyera’s new Topics functionality is built for the moment after classification, when teams have plenty of findings but still cannot answer what leadership needs: what matters most, what is urgent, and what gets fixed first.
Topics are an LLM-powered business context layer that uses classifications as signals, then evaluates intent and full-document context to map content to business concepts that teams actually use, like “M&A Planning”, “Pricing Strategy”, or “Customer Contracts”.
With Topics, security teams can:
- Bring their taxonomy to life in Cyera using plain-language definitions, internal terminology, and business-specific concepts
- Define new Topics as priorities change, without rebuilding complex rules
- Prioritize and act on risk in business terms instead of long lists of classifications
For example, a global enterprise found confidential merger planning documents shared via public OneDrive links. Cyera’s Topics surfaced the M&A theme (including an internal codename learned from context) and made the remediation target obvious.
Topics is not keyword matching, and it is not “searching your data and stitching together excerpts” to answer a prompt. It is intent- and context-based classification that turns signals into a decision-ready view of risk.
When your taxonomy matches the business, risk is easier to explain, easier to prioritize, and faster to remediate.
Classification Topics are generally available. Read the blog to learn more.
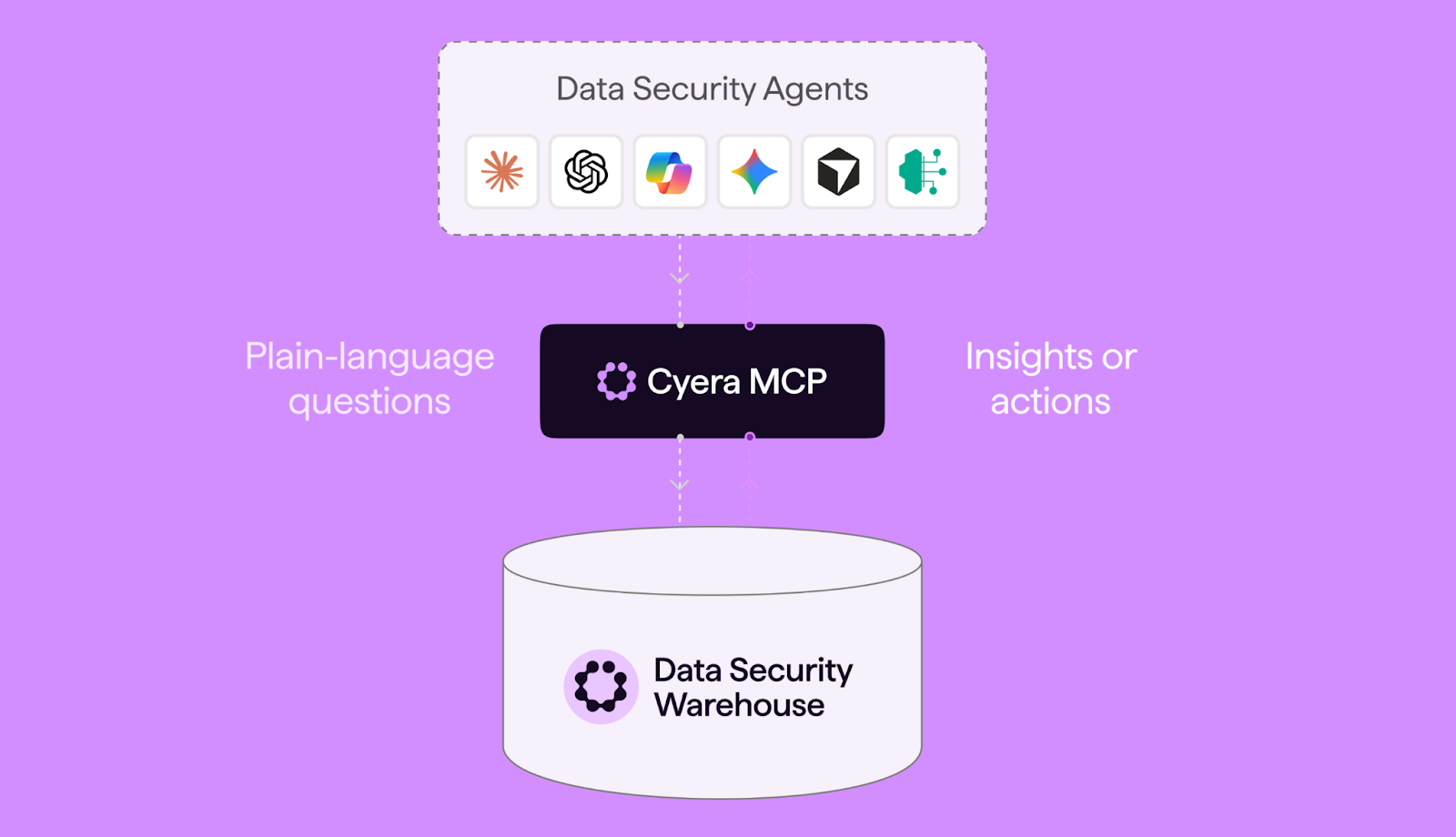
Cyera MCP: Build Your Own Data Security Agents
Security teams spend too much time assembling answers or completing workflows using scattered dashboards and manual queries. Cyera MCP changes that.
It's a Model Context Protocol server that lets AI tools, such as Claude, Cursor, Microsoft Copilot, ChatGPT, or custom-built agents, query Cyera's data security intelligence using plain language.
Instead of pivoting between tools, you ask a question: "Which data stores hold our most sensitive classified data?" or "Where does this individual's personal data appear across our environment?" The answer comes back structured, sourced, and ready to act on.
The use cases go beyond ad hoc queries. Security teams can build agents that continuously hunt for threats or flag and investigate issues such as sensitive datasets with overly broad permissions. SOC teams can automate operations and incident response. Leaders get executive reporting pulled directly from authoritative data with no manual assembly required.
Cyera MCP turns AI from a helpful assistant into an operational security tool, grounded in the data you already trust.
The MCP Server is generally available. Read the blog to learn more.
Cyera Privacy: Build Your Privacy Program in the AI era
Privacy programs have a problem. Outdated data. Major assumptions. Consent is difficult to track. Data subject requests (DSR) require information from many different sources. Data inventory is a spreadsheet or manual tool that reflects inaccurate processing activities the moment it’s finished. When a DSR request comes in or an assessment is needed, teams chase stakeholders and rely on best guesses.
That gap between privacy operations and the AI reality we now live in is where risk builds.
Cyera Privacy closes that gap by grounding privacy operations with ongoing data discovery and with enriched data classification. Teams operate from an up-to-date understanding of where personal data lives, how it’s used, and where risk exists.
Cyera Privacy offers a holistic solution for:
- Data Mapping. Keep your records of processing activities (RoPA) accurate as systems, SaaS apps, and AI tools evolve
- Privacy Assessments: Pre-fill assessments with real data and system context, including AI risk assessments.
- Data Subject Request (DSR) Automation: Streamline the full DSR lifecycle for every request, from intake to audit.
- Centralized Privacy Risk: Consolidate risk across systems, assessments, and AI usage into a single, prioritized view
- Consent Management: Build and deploy code-free consent collection points with automated enforcement across GDPR, CCPA, and more
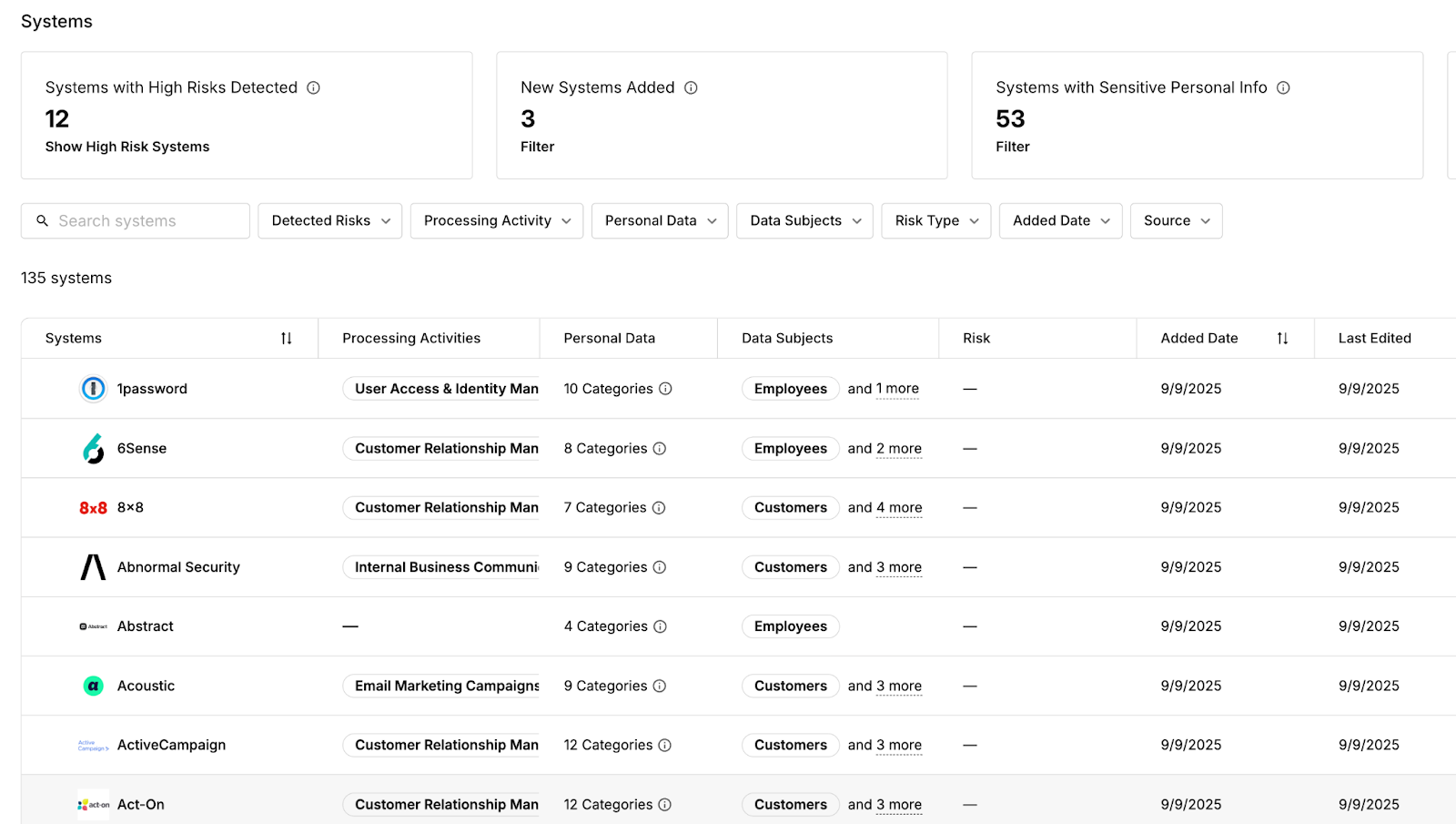
Also we’re enabling Cy for privacy, our AI agent that helps teams generate assessments, surface risks, and answer questions about their data environment using real system context, while keeping humans in control of every action.
Cyera Privacy is now generally available. Read the blog to learn more.
And more: Make Action Consistent and Auditable
None of this matters if teams cannot act on it consistently.
This release also includes improvements designed to help teams investigate faster, prioritize with confidence, and drive consistent action with clear accountability and audit trails:
- CNAPP Integration: Bring cloud posture signals together with sensitive data context to highlight misconfigurations tied to real exposure, reduce noise, and align cloud and data teams on what to fix first.
- AI Filters: Use plain-language intent to quickly narrow to the exposures that match a real scenario, improving triage and speeding audit, incident response, and executive asks with targeted, explainable filtering.
- Remediation Portal enhancements: Delegate issue resolution to the people closest to the data while keeping security in control through oversight, approvals, and auditability.
- Action Templates: Standardize common remediation motions into repeatable, guided responses so teams can reduce time-to-remediation, drive consistent outcomes across teams, and scale remediation by turning “what do we do next?” into an operational playbook.
- DLP Policy Recommendations Wizard: Stop tuning policies in the dark. Get AI-driven recommendations that tell you what to create, what to tune, and why, helping teams cut policy tuning cycles from months of guesswork to minutes of guided review.
All of this work only matters if teams can act repeatedly, consistently, and defensibly.
Security that moves at the pace of your data and AI
Data security spent two decades building walls around locations.
Data did not stay put.
Now AI makes movement the default across apps, identities, agents, and browsers. Security cannot rely on a static map of “known places” while data behaves like a dynamic system.
The shift is simple:
- See what AI sees
- Follow data across its lifecycle
- Express risk in business terms
- Act as fast as data moves
Your data already moves at the pace of AI.
Now your security can keep up.
If you want to see how these capabilities work together in your environment, request a demo today.
FAQs
Q.) How do I find shadow AI and secure prompts in the browser?
A.) Cyera Browser Shield provides real-time visibility and policy enforcement for browser-based AI tools. It can detect sensitive data in AI prompts at the point of entry and apply your policy action (for example, warn or block) so teams can govern AI usage without relying on users to self-police.
Q.) How can I track when a sensitive file was copied, downloaded, or shared and assess the blast radius during an incident?
A.) Cyera Data Lineage for Files helps security teams understand how sensitive files spread by connecting related copies and variants across environments. Instead of treating every download, share, and upload as an isolated event, File Lineage provides continuity so teams can scope exposure faster and understand where sensitive data propagated.
Q.) How can I prioritize data security risk in business terms (not just “PII”, “PCI”, and other technical labels)?
A.) Topics is an LLM-powered business context layer that uses intent and full-document context to map classified data to business concepts (and customer-defined taxonomy), such as M&A planning or customer contracts. This helps teams prioritize and govern risk in business terms instead of managing long lists of technical labels.
Q.) What is an MCP Server for security teams, and what can I do with it?
A.) The Cyera MCP Server provides a standardized way for security teams to build their own AI agents to accelerate investigations and automate security workflows. Analysts can query Cyera’s data using natural language and answer questions such as where sensitive data exists, how it’s classified, and what are the biggest risks.
Q.) How can I automate DSR/DSAR fulfillment and keep data mapping and privacy assessments accurate as data changes?
A.) Cyera Privacy is built on continuous discovery to keep privacy operations grounded in current data reality. It supports data mapping, privacy risk assessments pre-filled with system context, streamlined data subject request (DSR) workflows, and code-free consent management for regulations such as GDPR and CCPA.





.svg)