96% of Enterprise Permissions Go Unused. AI Agents Won't Leave Them That Way.

Cyera Research Joint Research with Oso
We analyzed 2.4 million workers and 3.6 billion permissions. What we found should change how every security team thinks about the age of autonomous AI.
This is the first empirical study of how enterprise permissions are actually exercised in production - not how they’re designed, not how policy says they should work, but what employees actually do with the access they’ve been given. The findings are unambiguous. And the implications, as AI agents enter the picture, are severe.

Finding 01
Almost no one is using their access. Almost everyone still has it.
Only 4 in 100 workers take any action at all in most enterprise applications over a 90-day period. The other 96 hold active credentials and never open the system. Among the 4% who do log in, they exercise just 17% of the permissions available to them. The other 83% sit dormant — live, functional, and waiting.

The exposure isn’t theoretical — it’s structural. 13% of the workforce can reach regulated data. 31% can modify or delete it. These permissions are permanently available, whether or not anyone ever uses them.
Finding 02
Over-provisioning is baked into how enterprise systems are built.
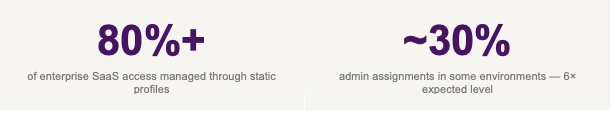
This isn’t an accident. Across enterprise SaaS environments, more than 80% of access is managed through static permission profiles - rigid bundles configured once and expanded over time as roles grow and integrations multiply. A quarter of users have no individual permissions at all; their entire access model is a profile that was set up years ago and never trimmed.
Admin access tells the same story. Best-practice governance benchmarks set administrative access at around 2–5% of users. Some environments we analyzed had assigned admin privileges to nearly 30% — six times the expected level, with high-privilege capabilities distributed far beyond any operational need.
Case Study: Cyera Research Deep Dive
Salesforce: where permission sprawl becomes a concrete, measurable risk
Everything described in this post plays out in sharp relief inside Salesforce — the CRM platform sitting at the center of most organizations’ customer data ecosystems. Cyera Research conducted a dedicated analysis of Salesforce environments across multiple organizations and found the numbers are worse than the enterprise average. Not because Salesforce is uniquely broken, but because it is uniquely central: the permissions it holds govern access to customer records, financial data, deals, contacts, and regulated information at scale.
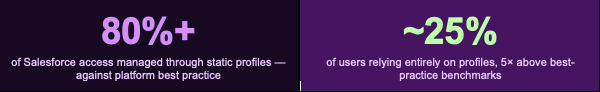
Salesforce itself recommends a modular access model: minimal profiles that define only baseline access, layered with permission sets for role-specific privileges. Production environments consistently invert this. Profile-heavy configurations make it harder to audit, harder to reduce, and much harder to reason about what any given user can actually do — let alone what an agent would do if it inherited their account.
The ‘nuclear buttons’: View All Data and Modify All Data
Within Salesforce, two permissions override the entire sharing model. View All Data grants unrestricted read access to every record in the org. Modify All Data goes further - providing read, write, and delete access across the entire environment, effectively elevating the holder to super-admin. Cyera Research found these capabilities distributed far more broadly than intended, in many cases persisting long after the original justification had passed. While most organizations held admin access to around 5% of users, several environments showed assignments reaching nearly 30%.

Salesforce access management isn’t a technical chore — it’s a strategic pillar of data governance. And as AI agents get connected to Salesforce environments, the governance gaps that have quietly accumulated become something far more urgent than a hygiene problem.
Are Your Salesforce Permissions Protecting You - or Exposing You?
The first in Cyera Research’s Salesforce Access Control Deep Dive series, covering profiles, permission sets, high-privilege capabilities, record-level access, and public data exposure.
The Inflection Point
Humans have always saved us from our own permissions. Agents won’t.
Until now, the risks above were largely theoretical. Human behavior has always acted as a natural ceiling:people work slowly, follow routines, and exercise a tiny fraction of their technical access. The 96% of permissions that go unused stay unused because people behave like people.
AI agents remove that ceiling entirely. They operate continuously, at machine speed, calling APIs directly with no natural stopping point. Theydon’t bring judgment or hesitation. When an agent inherits an employee’s permission set, it doesn’t inherit the small slice that employee typically uses. It inherits everything that employee technically could do —including the 96% that was never touched.
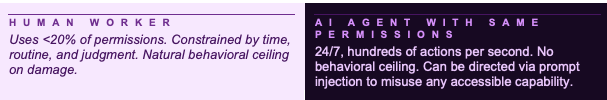
Over 40,000 agent instances have been found running malicious community-contributed integrations. An attacker doesn’t need stolen credentials — just malicious instructions in content the agent processes. That dormant 96% becomes an active attack surface, instantly.
"When agents are handed broad, static permissions, the unused ones quietly expand the attack surface. What teams need are identity systems that keep agent actions tightly scoped and tied back to human intent."
Nancy Wang - CTO, 1Password
What to do
The window is open. It won’t stay that way.
The good news: when 96% of permissions go unused, there is massive risk reduction available without disrupting anything. Access that no one exercises can be revoked without anyone noticing. Profiles that are over-provisioned can be tightened before an agent ever touches them.
The organizations that get ahead of this treat access governance as infrastructure - not a compliance checkbox. Before any agent deployment: audit what’s actually being used. Provision dedicated agent identities scoped to the specific task, not inherited from human accounts. Start in read-only mode. Log every action from day one. Triage by blast radius - modify, delete, and export permissions first.
"With agents, risks compound exponentially. Broader surface area, more secrets, more over-privilege than ever before." -
Armon Dadgar — Co-Founder & CTO, HashiCorp
Agents are moving from pilot to production now. Every day with an un-audited permission model is a day closer to that model being inherited by something that will use all of it.
Cyera Research & OSO: Full Report
2.4M workers, 3.6B permissions, 10 actions to close the gap.
Download the complete findings
About Cyera Research
Cyera Research is the data-centric research arm of Cyera, dedicated to advancing vulnerability research and transforming real-world data insights into decisive security action. Led by a multidisciplinary team of researchers, scientists, security engineers, and security vulnerability researchers, they uncover critical vulnerabilities, emerging attack vectors, and AI-driven risks across modern data environments. By combining hands-on vulnerability discovery with rigorous, evidence-based research, Cyera Research delivers actionable intelligence and practical guidance that empower organizations to proactively secure, govern, and protect their data and AI assets with confidence.
.avif)
.png)



.svg)