Claw Chain: Cyera Research Unveil Four Chainable Vulnerabilities in OpenClaw
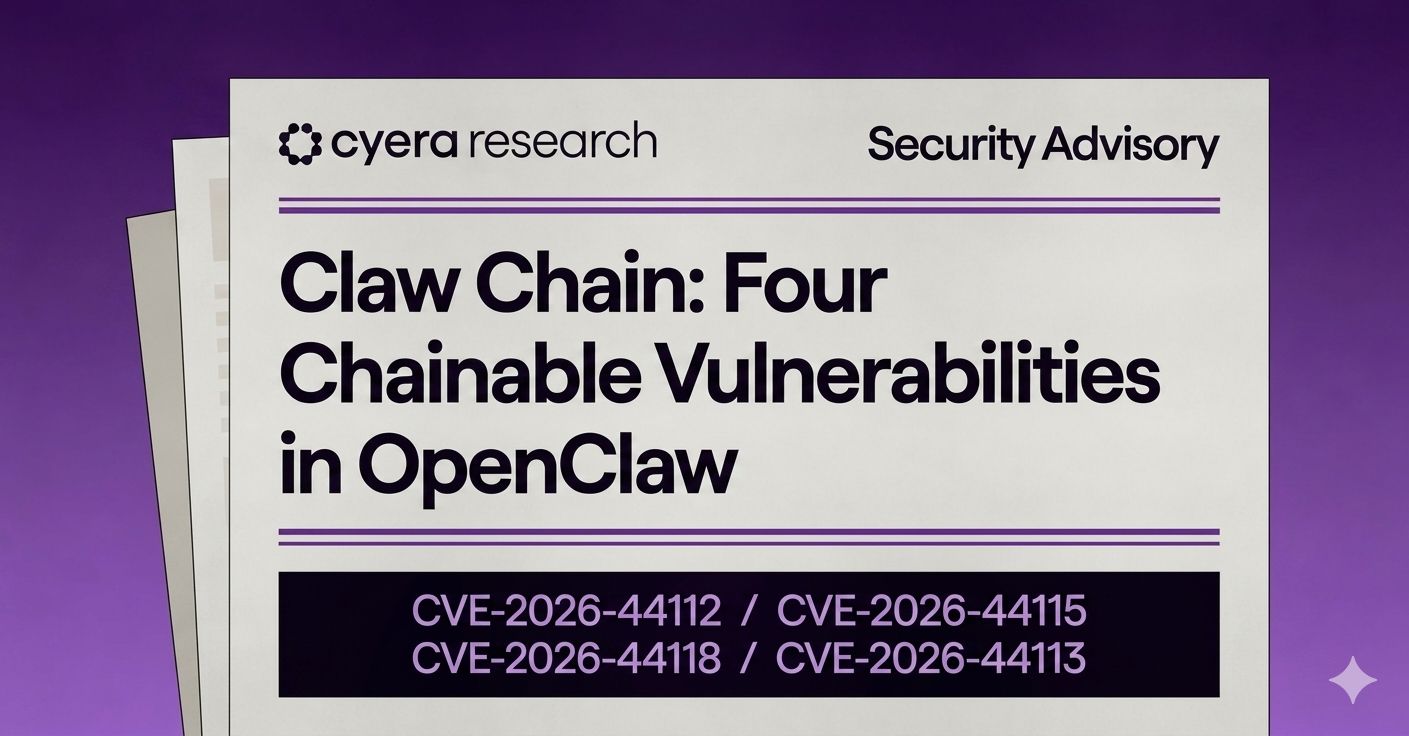
Vulnerability Class: Sandbox escape, privilege escalation, data exposure
CVE IDs: CVE-2026-44112, CVE-2026-44115, CVE-2026-44118, CVE-2026-44113
Highest CVSS Score: 9.6 — CRITICAL (CVE-2026-44112)
Affected Product: OpenClaw (all versions prior to April 23, 2026 patches)
Attack Vector: Agent-mediated — prompt injection, malicious plugin, supply-chain input
Exposed Instances: ~65,000 (Shodan) · ~180,000 (Zoomeye) public-facing OpenClaw servers
Discovered By: Cyera Research
What We Found
Cyera's research team identified four previously undisclosed vulnerabilities in OpenClaw, one of the most rapidly adopted open-source platforms for autonomous AI agents. Originally launched as “Clawdbot” in late 2025, OpenClaw connects LLMs directly to filesystems, SaaS applications, credentials, and execution environments - and is increasingly deployed across enterprise workflows for IT automation, customer service, and operational integrations with platforms like Telegram, Discord, and Microsoft Agent 365.
The four findings - spanning sandbox isolation, identity, and execution validation - were disclosed to the OpenClaw maintainers in April 2026 and have all been patched.
Their combined impact points to a deeper concern: AI agents have become a primary execution surface, and the security model around them has not caught up
The Vulnerabilities
CVE-2026-44112 - TOCTOU Filesystem Write Escape CRITICAL · 9.6
A time-of-check / time-of-use race condition in the OpenShell sandbox lets attackers redirect writes outside the sandbox boundary - enabling configuration tampering, backdoor placement, and persistent control of the host. The agent's automated write behavior amplifies impact at runtime.
CVE-2026-44115 - Execution Allowlist Env-Vars Disclosure HIGH · 8.8
A gap between OpenClaw's command validation and shell execution allows environment variables - including API keys, tokens, and credentials - to be expanded inside unquoted heredocs, returning sensitive data through commands that appear safe at validation time.
CVE-2026-44118 - MCP Loopback Privilege Escalation HIGH · 7.8
OpenClaw trusts a client-controlled ownership flag (senderIsOwner) without validating it against the authenticated session. A locally executing process with a valid bearer token can elevate itself to owner-level privileges and gain control over gateway configuration, cron scheduling, and execution environment management.
CVE-2026-44113 - TOCTOU Filesystem Read Escape HIGH · 7.7
The same race-condition pattern in read operations lets attackers swap a validated file path with a symbolic link pointing outside the allowed mount root - exposing system files, credentials, and internal artifacts the agent was never meant to reach.
The Attack Chain
The four vulnerabilities are individually meaningful, but their combined effect is the more important story. From a single supply-chain-style foothold, an attacker can chain three of them in parallel from one entry point:
STEP 1
Foothold: A malicious plugin, prompt injection, or compromised external input gains code execution inside the OpenShell sandbox.
STEP 2
Data Exfiltration: TOCTOU read escape (CVE-2026-44113) and env-var disclosure (CVE-2026-44115) expose credentials, secrets, and sensitive files beyond the agent's intended scope.
STEP 3
Privilege Escalation: MCP loopback flaw (CVE-2026-44118) elevates the compromised process to owner-level control of the agent runtime.
STEP 4
Persistence: TOCTOU write escape (CVE-2026-44112) plants backdoors, modifies configuration, or alters future agent behavior.
The AI Security Implication
Attackers can exploit the AI agent itself to execute the attack chain.
By weaponizing the agent's own privileges, an adversary moves through data access, privilege escalation, and persistence - using the agent as their hands inside the environment. Each step looks like normal agent behavior to traditional controls, broadening blast radius and making detection significantly harder.
What Is the Impact
OpenClaw agents typically operate with broad access to internal systems, credentials, and SaaS data - often with weaker governance than the systems they connect to.
With ~65,000 (Shodan) and ~180,000 (Zoomeye) publicly accessible OpenClaw instances as of May 2026, this exposure surface is immediate and broad.
What an Attacker Can Steal or Achieve
FROM THE AGENT RUNTIME:
- Environment variables (API keys, tokens, secrets)
- Bearer tokens and authentication material
- Internal configuration and runtime artifacts
FROM THE HOST FILESYSTEM:
- Sensitive files reachable outside the sandbox
- System credentials and configuration files
- Internal source code and documentation
THROUGH AGENT PRIVILEGES:
- Data accessible via connected SaaS / enterprise systems
- User prompts, outputs, and conversation history
- Privileged operations (scheduling, gateway, execution)
Who Is Most at Risk
- Enterprises using OpenClaw for IT support, business workflow automation, or customer-service agents.
- Development teams integrating OpenClaw with messaging platforms (Telegram, Discord, Slack), enterprise systems, or agentic tooling like Microsoft Agent 365.
- Organizations in regulated industries - financial services, healthcare, legal - where agent prompts and outputs may include PII, PHI, or privileged data.
- Any deployment where OpenClaw is exposed to the public internet without authentication or network controls in front of it.
What You Should Do
Organizations running OpenClaw should treat this as a Priority 1 advisory and take the following actions:
Immediate Actions (Within 24 Hours)
- Patch OpenClaw. Apply the April 23, 2026 fixes covering GHSA-5h3g-6xhh-rg6p, GHSA-wppj-c6mr-83jj, GHSA-r6xh-pqhr-v4xh, and GHSA-x3h8-jrgh-p8jx.
- Identify exposed instances. Use asset inventory or external scanning (Shodan, internal recon) to locate any internet-facing OpenClaw deployments and place them behind authentication or firewall controls.
- Rotate secrets. Assume any environment variable or credential reachable by OpenClaw processes may be compromised. Rotate API keys, tokens, and bearer credentials immediately.
Short-Term Hardening (Within 1 Week)
- Audit agent access. Map what data, credentials, and systems each OpenClaw agent can reach. Reduce scope aggressively.
- Treat agents as privileged identities. Apply the same access scoping, monitoring, and lifecycle controls used for service accounts.
- Review supply chain inputs. Audit plugins, prompts, and external inputs feeding agent workflows. Restrict installation rights and require review for new plugins.
- Network segmentation. Place OpenClaw deployments on isolated network segments with strict egress controls to limit exfiltration paths.
How Cyera Can Help
Cyera's data security platform gives organizations the visibility and control needed to assess exposure from agentic AI vulnerabilities like Claw Chain - and to prevent data exfiltration across AI workloads.
Data Discovery & Classification
Identify sensitive data flows into AI agent systems - including what data OpenClaw agents and their plugins can reach. Cyera continuously maps where PII, credentials, proprietary code, and regulated data exist across your environment, so you know exactly what is in scope when an agent is compromised.
AI Risk Posture Assessment
Assess your organization's exposure to agentic AI infrastructure vulnerabilities. Cyera can identify unauthenticated or misconfigured AI agent endpoints, flag publicly exposed OpenClaw instances, and provide a risk-prioritized remediation roadmap.
Data Loss Prevention for AI Workloads
Enforce policies that prevent sensitive data from being submitted to or processed by AI agent endpoints without authorization. Cyera's DLP capabilities extend to agentic pipelines and developer tooling, ensuring outputs cannot be silently exfiltrated.
Threat Detection & Incident Response
Detect anomalous access patterns and data movement consistent with agent-layer exploitation of vulnerabilities like Claw Chain. Cyera's threat intelligence helps security teams investigate potential past exposure and understand the blast radius of an agent compromise.
For the full technical breakdown go to: cyera.com/research
.avif)
.png)
.png)

.svg)