Access Trail
Know who accessed data.
Stop who shouldn’t.
Your data access detective
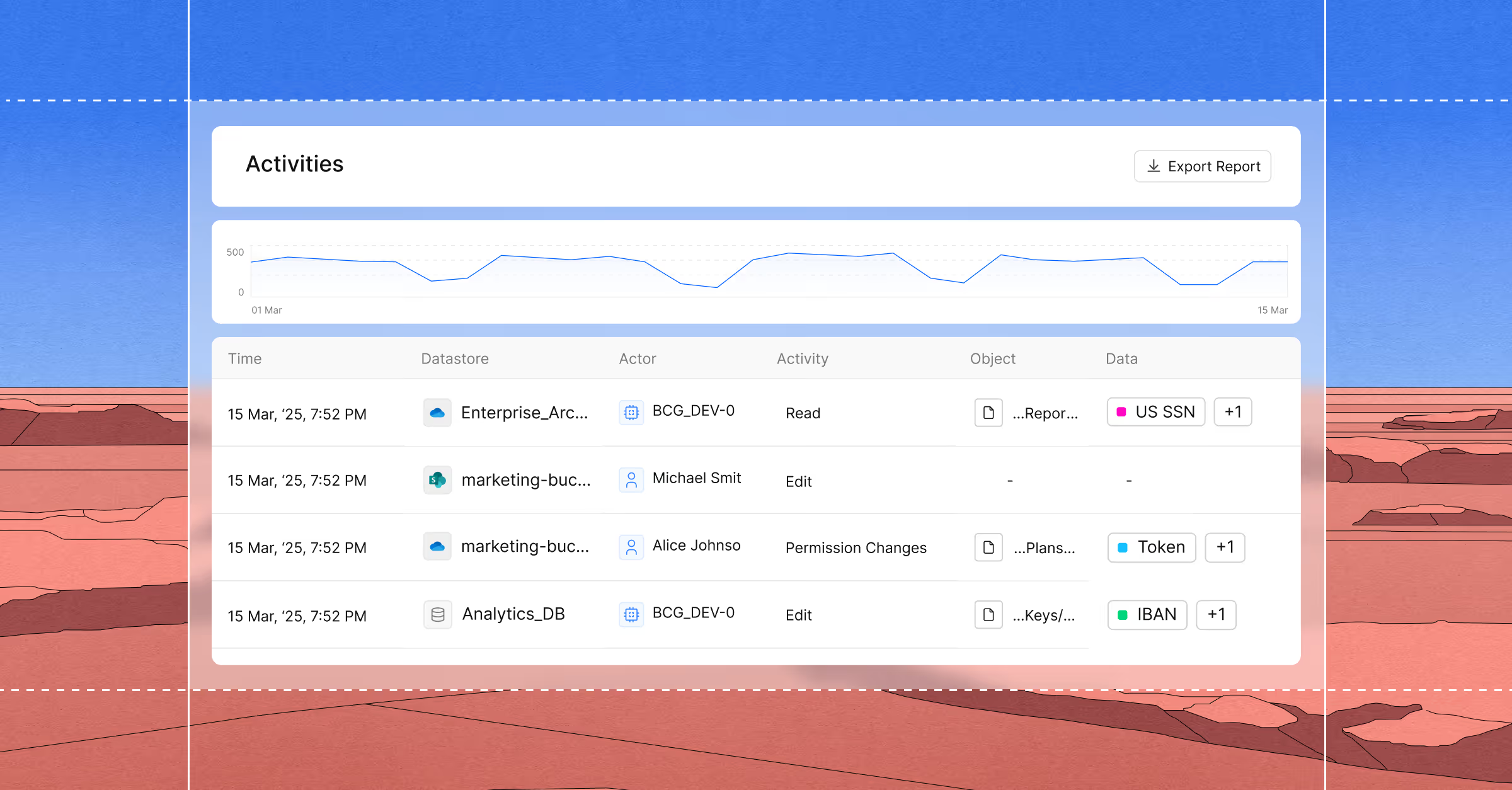
Access auditing collapses when you can’t see what data is actually involved, leaving teams buried in noise. Cyera Access Trail cuts through the clutter by tying every access event to the right data and the right identity – human or AI – enabling confident auditing and targeted remediation.
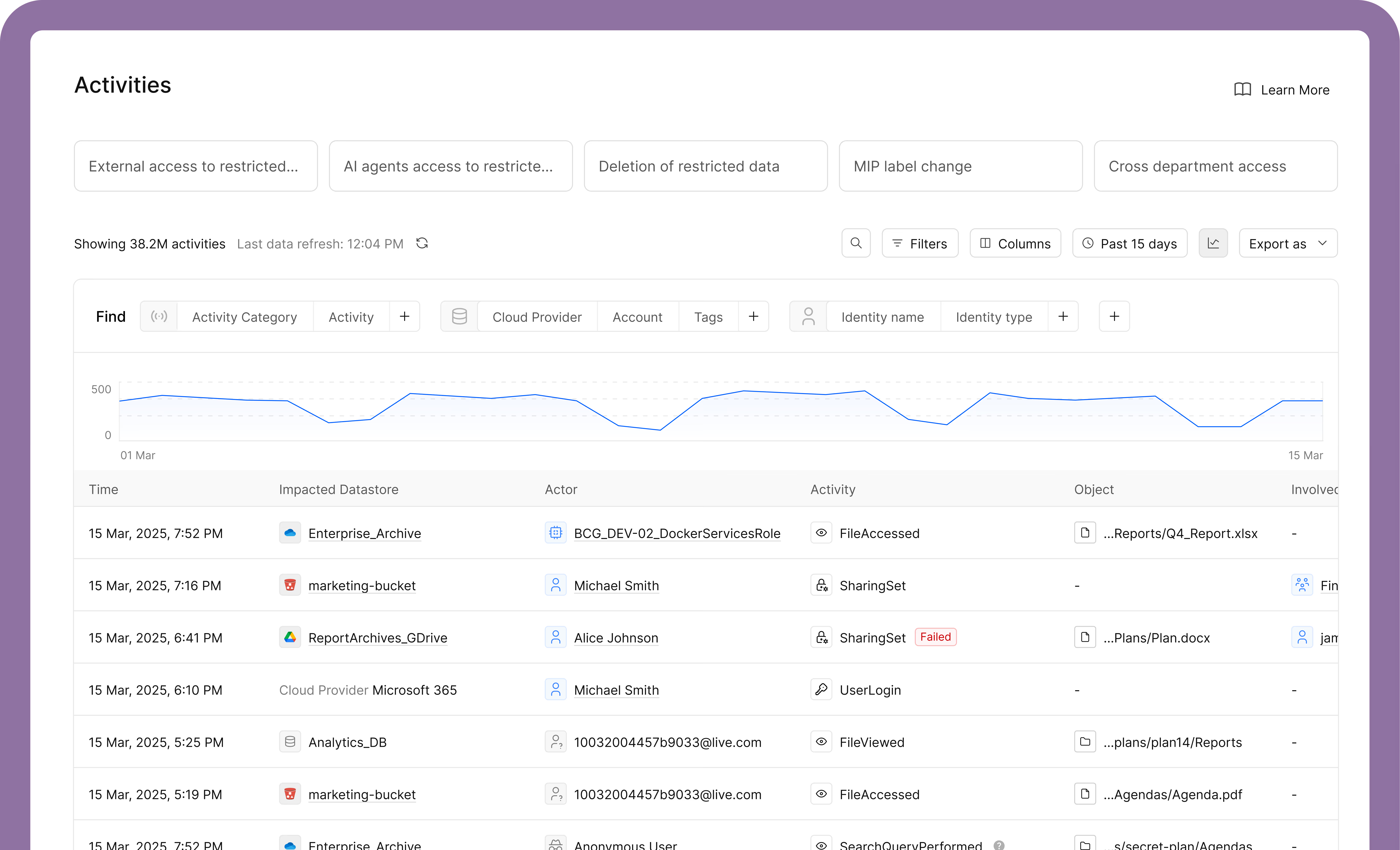
Capture access activities in one place
Illuminates every human, system, and AI touchpoint with sensitive or proprietary data so you always know what happened, when, and by who.
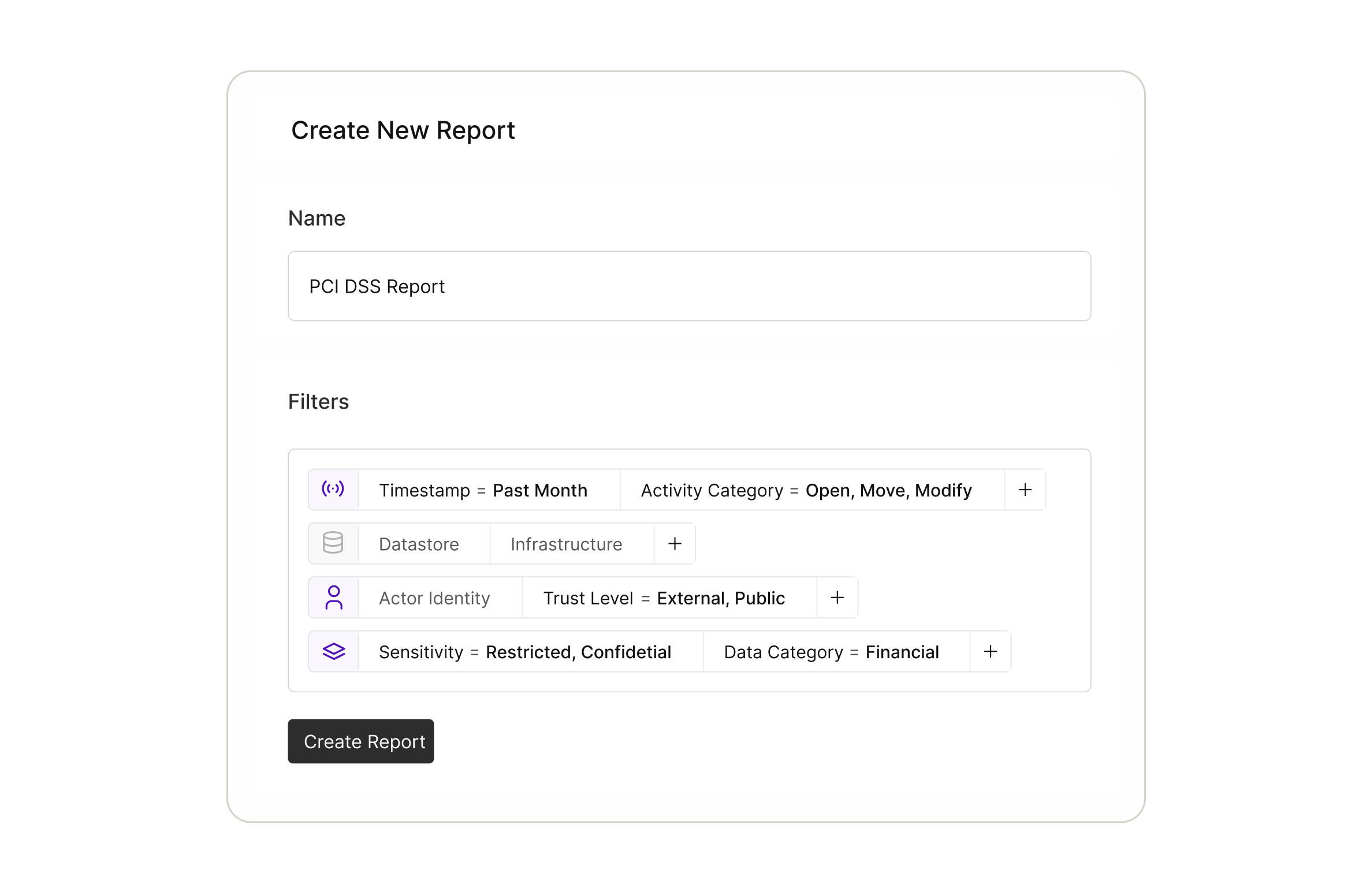
Gather audit evidence with ease
Tracking down compliance evidence shouldn’t be a scavenger hunt. Quickly find exactly what auditors ask for, with a full year of audit records ready when you need them.
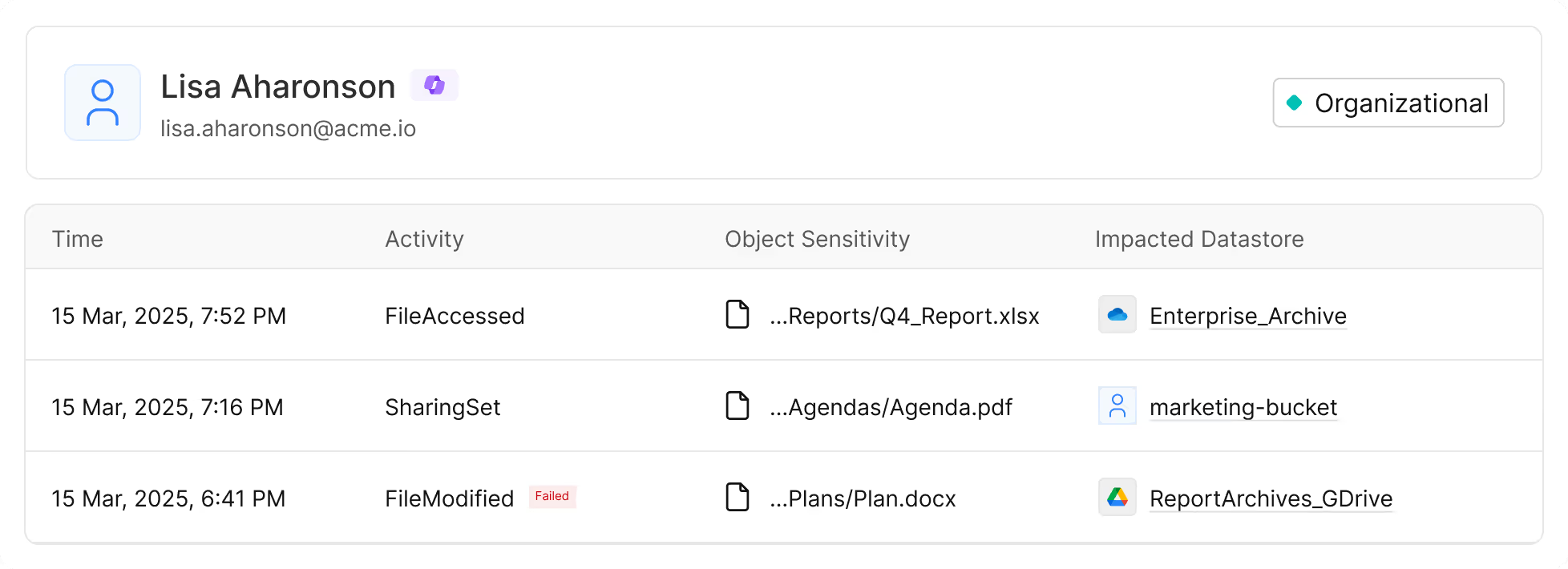
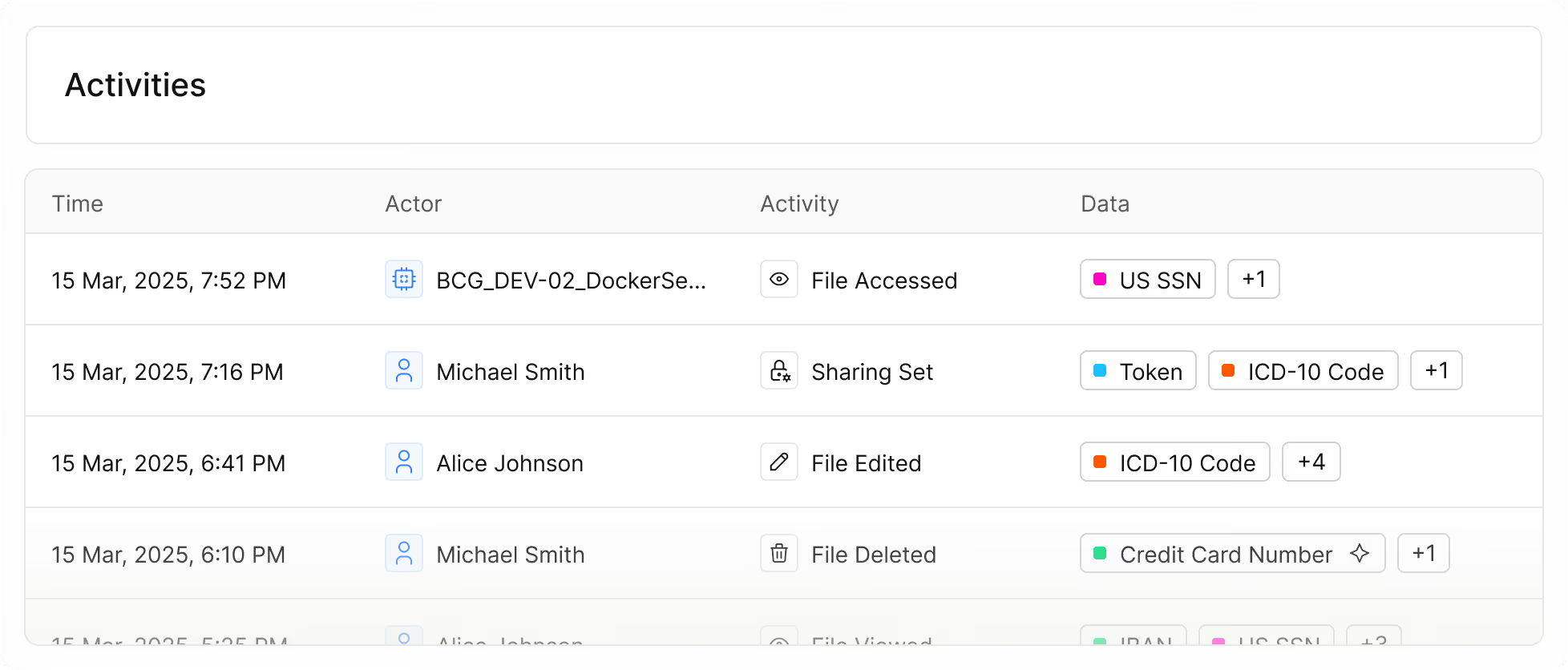
Speed up insider threat response
Risky behavior blends in with normal activity until it is too late. Investigate and remediate insider risks faster and more efficiently by correlating activities with identities and data classifications in context.
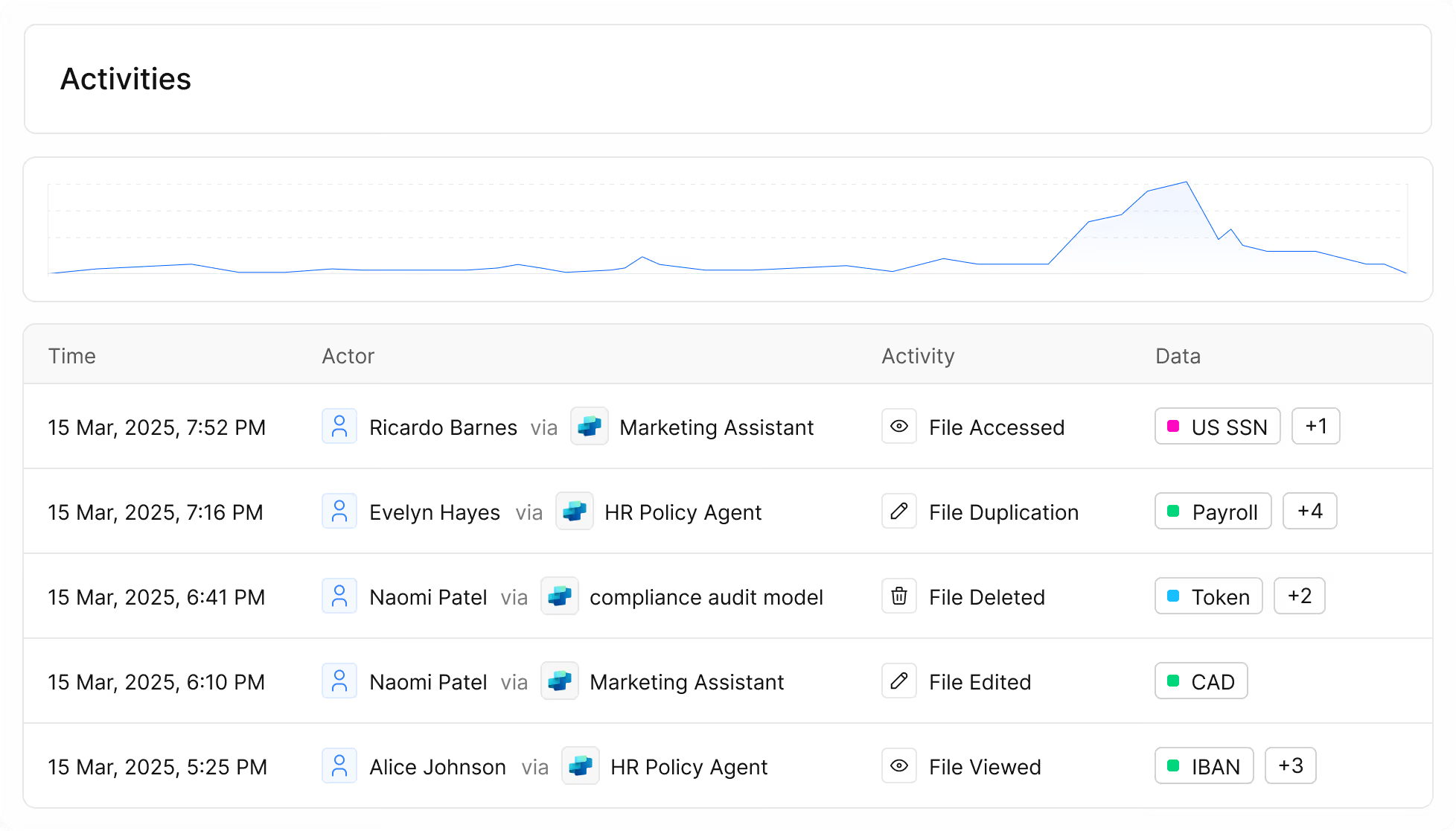
Monitor how AI uses your data
AI data access shouldn’t run wild. Reveal how AI tools and agents interact with information so you can maintain control and trust as AI becomes part of daily work.
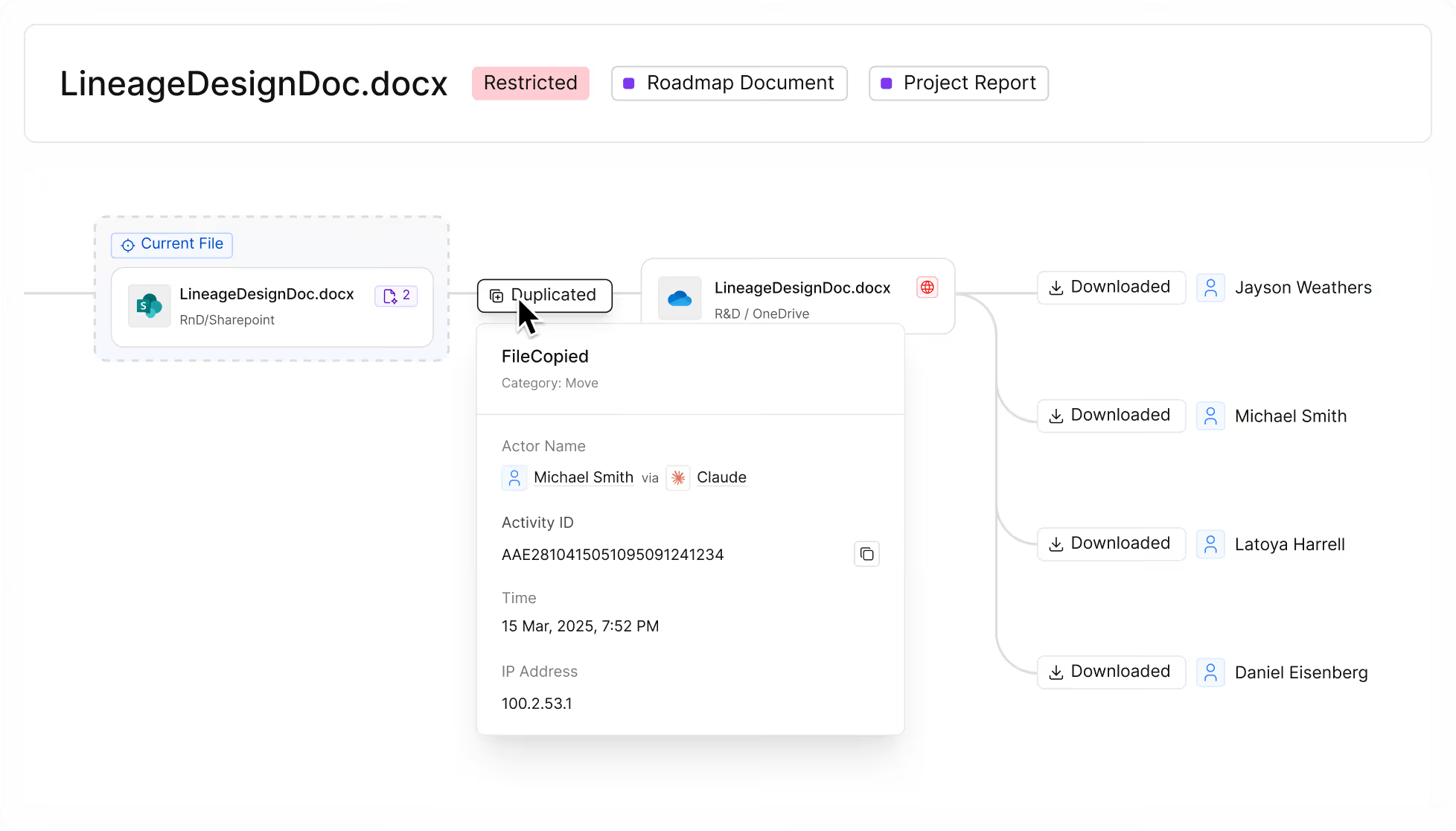
Trace the lineage of sensitive files
When incidents happen, context is everything. Data Lineage provides visibility into the complete file journey across copies and derivatives, helping accelerate investigations, uncover hidden data sprawl, and remediate with confidence.
Cyera Named a Leader in The Forrester Wave™: Sensitive Data Discovery And Classification Solutions, Q2 2026
.avif)

One platform.
Explore more Cyera products.
Identify and label data in discovered datastores with relevant data classes, and use context to determine the criticality of.
FAQs
Cyera Access Trail is a data access auditing and monitoring solution that captures every interaction with sensitive data across humans, systems, and AI agents. It combines deep, AI-native data classification with identity context to show who accessed what data, when, how, and why, delivering a complete, continuous activity trail. This enables security and compliance teams to understand data access in real time, investigate incidents quickly, enforce least-privilege, and support audits with automated, verifiable evidence rather than manual logs.
Access Trail fills visibility gaps that traditional tools leave behind by tracking actual access events, not just permissions. With one-year retention of detailed access logs, teams can generate audit-ready evidence, demonstrate compliance with regulatory requirements, and replace manual reporting processes with automated workflows. It also helps detect insider misuse, uncover excessive rights, and show how AI tools interact with sensitive data, giving security leaders the proof they need for control effectiveness and governance.
Modern environments include both human users and AI systems that interact with data. Access Trail tracks and logs every access event from AI tools and autonomous agents, correlating those actions with data sensitivity, ownership, and business context. This lets security teams see how generative AI and automation platforms consume or transform sensitive data, identify risky behaviors or misuse, and ensure AI interactions follow compliance and governance policies. Monitoring AI access in context is critical as adoption accelerates and blind spots widen in complex data ecosystems.
Access Trail supports core security and governance functions including insider risk investigations, audit readiness, continuous compliance, access rightsizing, and data ownership validation. It lets teams rewind historical activity to investigate incidents, detect abnormal access patterns in near real time, and automatically correlate events with contextual data like location, retention settings, and sensitivity. It also surfaces unused entitlements for least-privilege enforcement and helps minimize data sprawl by showing actual usage versus theoretical access.
Unlike basic access logs, which often lack business context, data sensitivity, and identity correlation, Access Trail automatically enriches raw activity with classification and identity insights. This transforms millions of events into actionable intelligence, reduces false positives, and provides an auditable, continuous view of data interactions. Traditional tools typically offer point-in-time snapshots, while Access Trail persists a full year of detailed activity, enabling faster investigations, stronger governance, and continuous assurance rather than periodic checks.






















.svg)