Introducing Data Lineage: Trace how humans and AI move, transform, and propagate sensitive files
Visualize all interactions throughout a file's lifecycle. Investigate data security incidents faster. Roll out AI with confidence.
Key Takeaways
- Data spreads fast through copy, rename, transform, and share, and point-in-time tracking misses the full path.
- AI multiplies sensitive files into new versions and artifacts, creating bigger visibility gaps.
- Cyera Data Lineage reconstructs end-to-end file lifecycles across human and AI activity in one view for faster investigations and containment.
- Turns alerts into root-cause context across systems and transformations, so teams can prevent repeat exposures, not just remediate symptoms.
Enterprise data doesn’t sit still. Files are copied, renamed, transformed, and shared across teams in seconds. AI makes file propagation across systems even harder to track. Yet, most security teams are still piecing together individual logs and endpoint activity to understand how incidents transpire.
When you lose sight of how data moves, you lose control over risk. During an investigation, security teams need to understand not just what happened, but what led to it and what followed. Where did the file originate? How did it evolve? Was it copied, shared, or propagated beyond its intended location?
Reconstruct the Complete File Lifecycle for Security Analysis
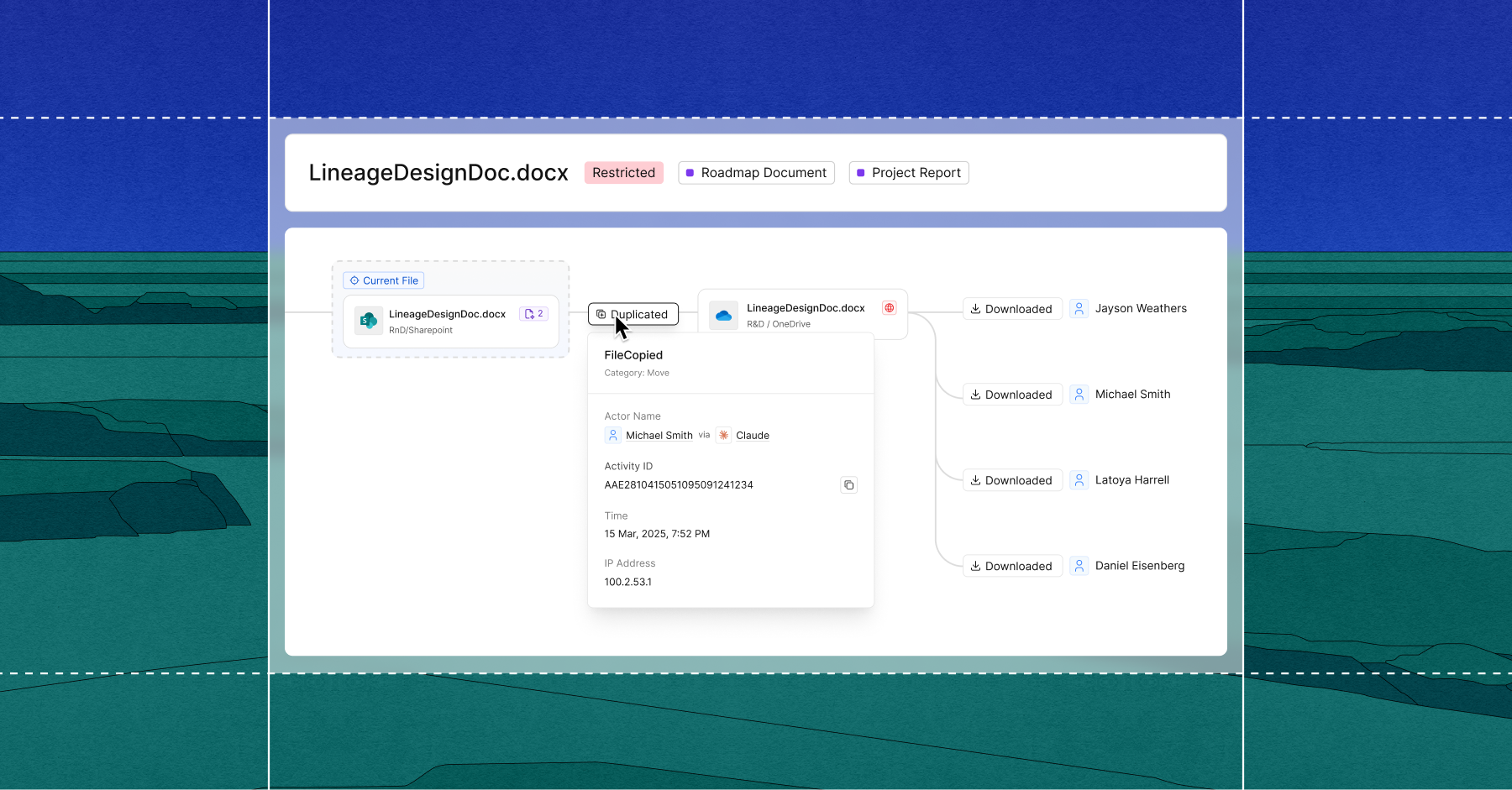
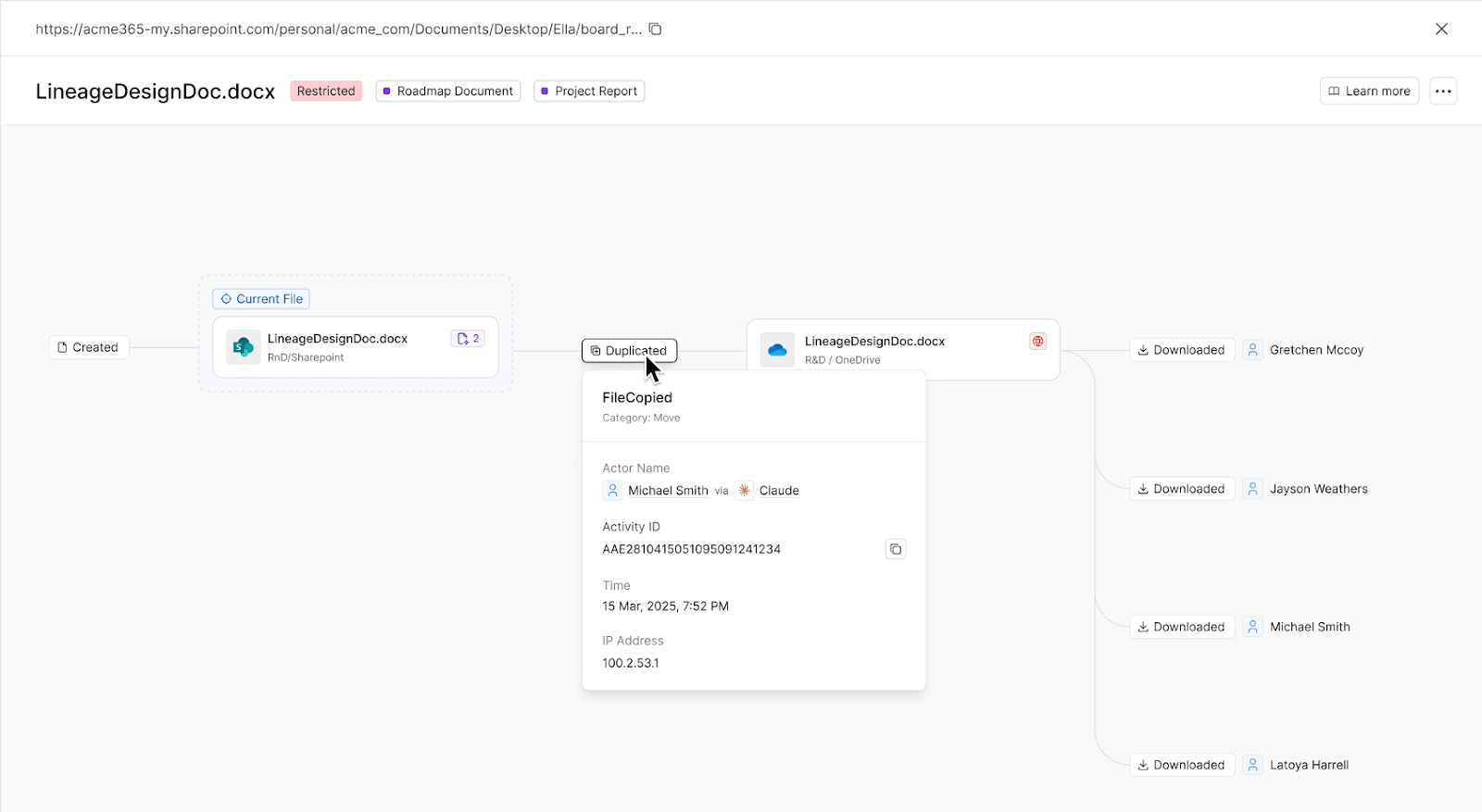
Cyera’s Data Lineage provides clarity into the entire lifecycle of files in a single, investigation-ready view. Built into existing Cyera workflows, teams can pivot from a single file to a complete propagation map showing how humans and AI access, download, transform, and share sensitive data within and across environments. This immediate understanding of file movement enables proactive, more informed investigations and targeted risk containment.
How Data Lineage Provides Investigation Context
When an alert fires, teams need to quickly understand whether the activity reflects real risk or normal business behavior. Data Lineage lays out the entire chain of events, revealing how data moved, who was involved, and where risk emerged. With full context around intent and propagation, analysts can rapidly assess impact and take action with confidence.
For example, a Cyera Access Trail event reveals unusual after-hours access to a confidential board report from a personal device. Instead of stopping at the access event, teams can dig into Data Lineage and see the full chain of activity: the report was copied to a personal OneDrive, renamed, and later downloaded by an external identity. What initially appeared to be a single suspicious login is quickly understood as expanded exposure, enabling the team to escalate, revoke access, and contain downstream copies before further spread.
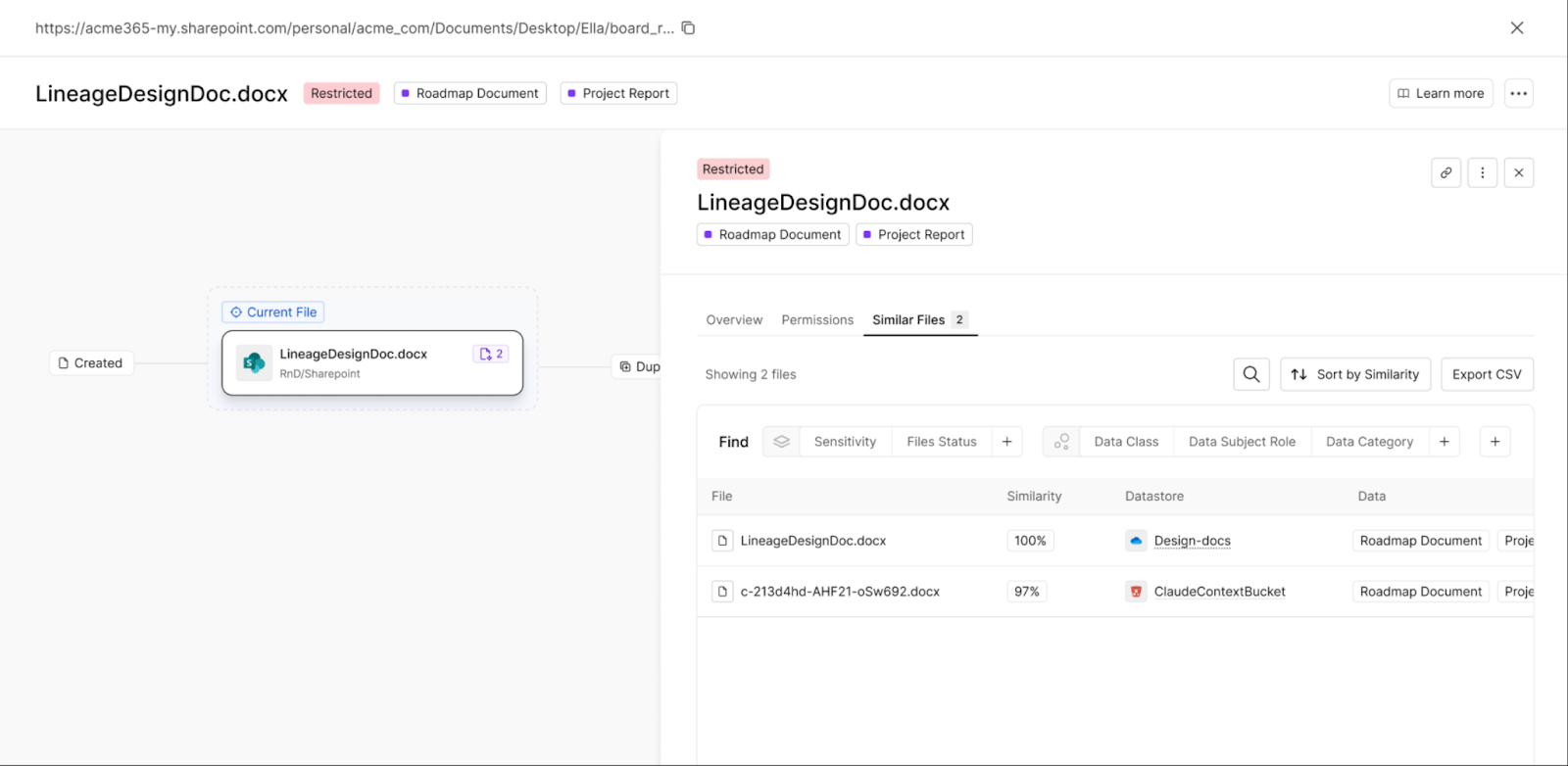
Maintaining Data Visibility Across System Boundaries
Audit trails are disrupted when files cross systems, change formats, or are transformed by AI tools. Data Lineage closes that gap with file similarity analysis based on Cyera’s AI-native DSPM insight, linking related versions across environments even without a direct activity trail.
This approach enables true cross-platform visibility. When data moves from SharePoint to Google Drive, or when an AI system generates a new artifact from sensitive content, Data Lineage connects those files back to their source. Even without a continuous audit chain, the propagation path can be reconstructed to expose intent and accelerate incident resolution.
Move from Tactical Remediation to Strategic Risk Mitigation
Investigators often find themselves correcting the same issue over and over: Removing a public link, revoking user access, or quarantining files. But these quick fixes may only address the symptom, not the source of the issue.
Consider Microsoft Copilot automatically generating summaries of confidential documents and saves them to an open team drive. Security removes one public link, only for another to appear days later. The alerts seem isolated, but the root cause is the same workflow.
With Data Lineage, teams trace each exposure back to that Copilot process. Instead of chasing individual links, they can adjust permissions or restrict how Copilot handles sensitive content, preventing the issue from recurring.
See the Full Story. Understand the Risk.
AI does not just access sensitive data, it multiplies it. A single file can quickly proliferate into summaries, derivatives, and downstream artifacts across clouds.
By connecting every copy and AI-generated output into one continuous narrative, Data Lineage reveals how risk began, how it spread, and where it must be contained. With that visibility, security teams move from reactive fixes to confident control over risk.
Data Lineage is in beta. To see it in action, request a demo today.
Data Lineage for Files FAQs
Q.) How does data lineage help with security investigations?
A.) Data lineage provides complete visibility into file movement, showing not just what happened during an incident, but the full chain of events that led to it and followed, enabling faster and more informed security responses.
Q.) What makes AI file propagation harder to track than human activity?
A.) AI systems can rapidly copy, transform, and move files across multiple environments in ways that traditional monitoring tools cannot easily follow, creating visibility gaps that data lineage solutions address.
Q.) How does Cyera Data Lineage integrate with existing security workflows?
A.) The solution builds directly into existing Cyera workflows, allowing security teams to pivot seamlessly from individual Access Trail events to complete propagation maps without switching between multiple tools or interfaces.
Q.) What happens when files cross system boundaries or change formats?
A.) Traditional audit trails often break when files move between systems or undergo transformation, but data lineage maintains continuity by tracking the relationships and connections across these boundaries.
Q.) How quickly can teams assess whether an event represents real risk?
A.) With complete context around data movement, user intent, and propagation patterns, analysts can rapidly determine if activity reflects genuine threats or normal business operations, reducing investigation time significantly.




.svg)